Hybrid Attack Paths, New Views and your favorite dog learns an old trick
Introducing Hybrid Attack Paths
When we introduced Azure Attack Paths into BloodHound, they were added as a completely separate sub-graph. At no point did Active Directory (AD) and Azure connect within a BloodHound dataset. Ever since adding Azure (honestly, even before that), we’ve wanted to solve that problem. We’re so very excited to introduce the first version of what we’ve taken to calling a “hybrid path” into BloodHound!
Microsoft Entra Cloud Sync and Microsoft Entra Connect Sync allow administrators to synchronize users from on-premises AD domains up to Entra ID tenants. Additionally, administrators can choose to enable a feature called “Password Hash Synchronization”, which replicates the password hashes from the on-premises user up to its Entra ID counterpart. This allows users to authenticate to Entra/Azure resources using their on-premises AD User Principal Name (UPN) and password. This creates Attack Paths from on-premises AD to Entra ID.
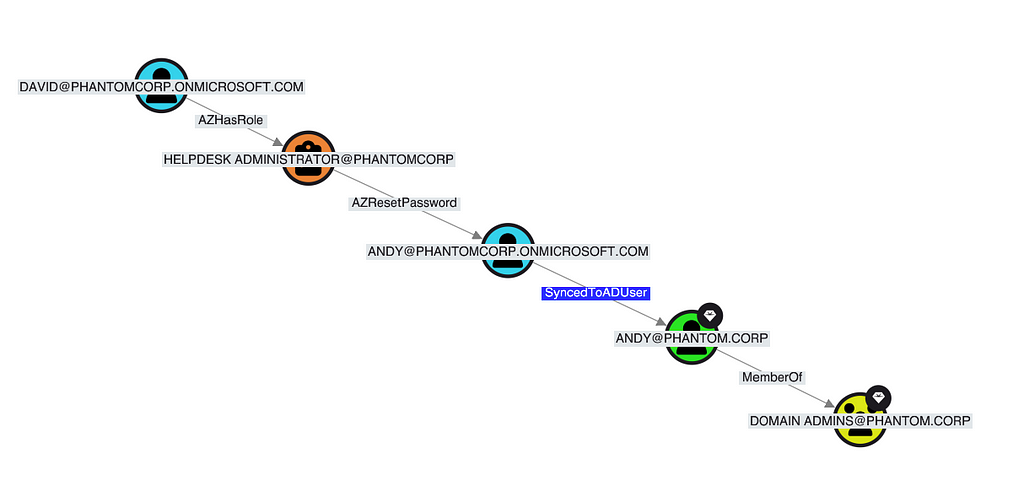
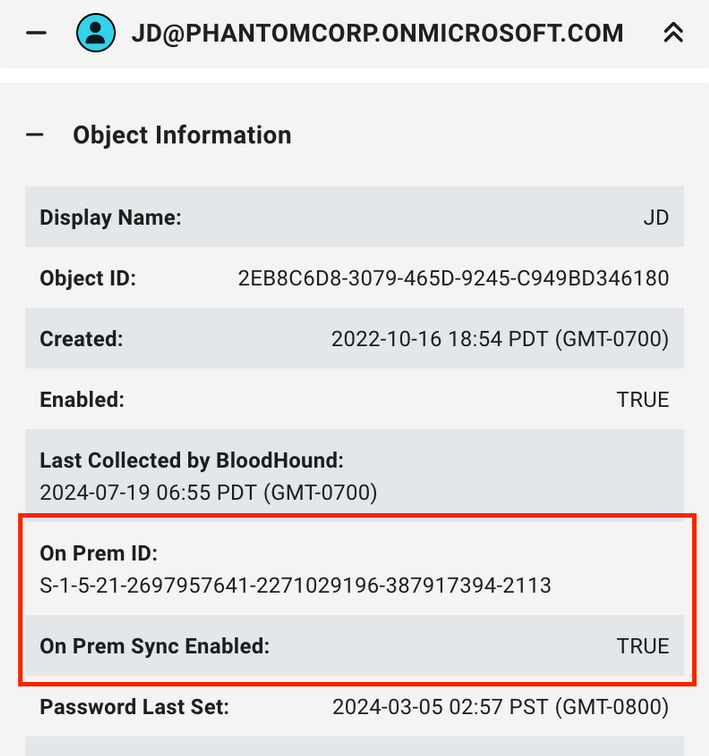
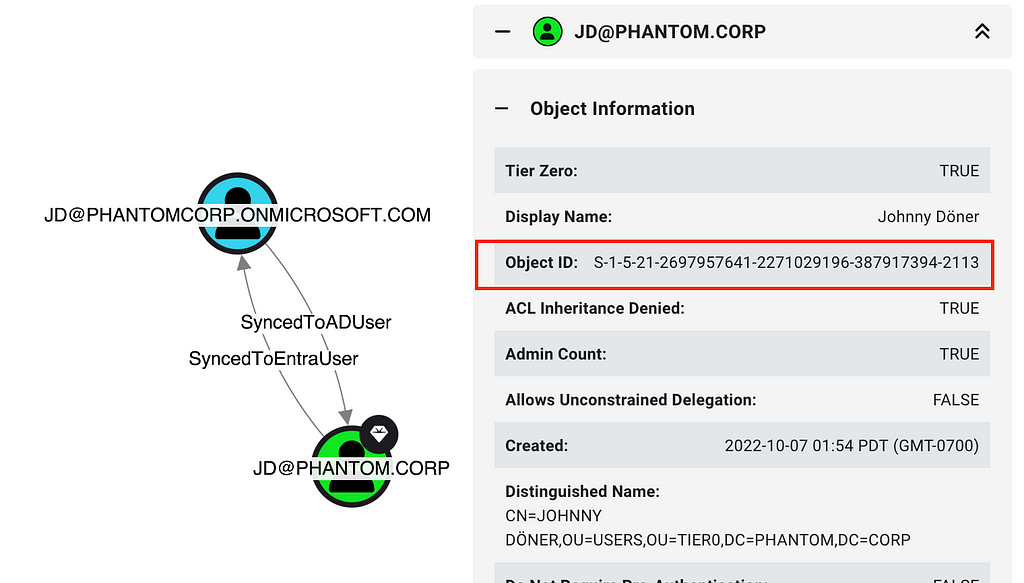
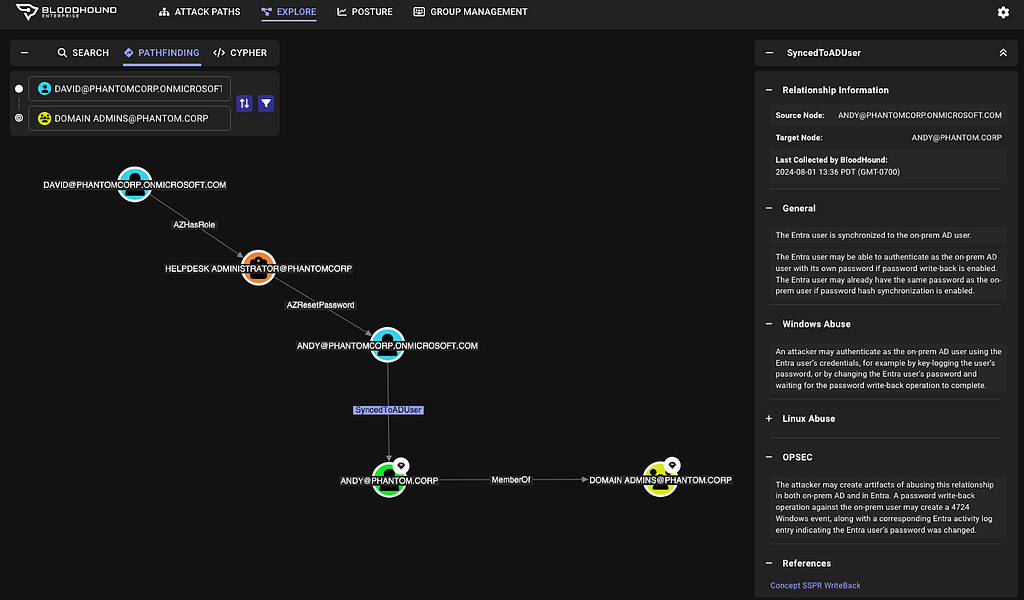
As of BloodHound v5.13.0, when data is collected from an Entra ID tenant as well as an AD domain with users synced between them, BloodHound will automatically generate Hybrid Attack Paths in the graph. Conveniently named “SyncedToADUser” and “SyncedToEntraUser”, these edges indicate where two objects are effectively equivalent; generally meaning that control of one grants control of the other. These edges are generated utilizing the “onpremsyncenabled” and the “onpremid” properties that result from an AzureHound collection. If an Entra ID user object is described as being synced (indicated by a “True” value in the “onpremsyncenabled” field), an edge will be added between the Entra ID user and the AD user identified in the “onpremid” field.
In the below screenshots, you can see the JD Entra ID user has sync enabled with an associated Object ID of the JD AD object displayed.
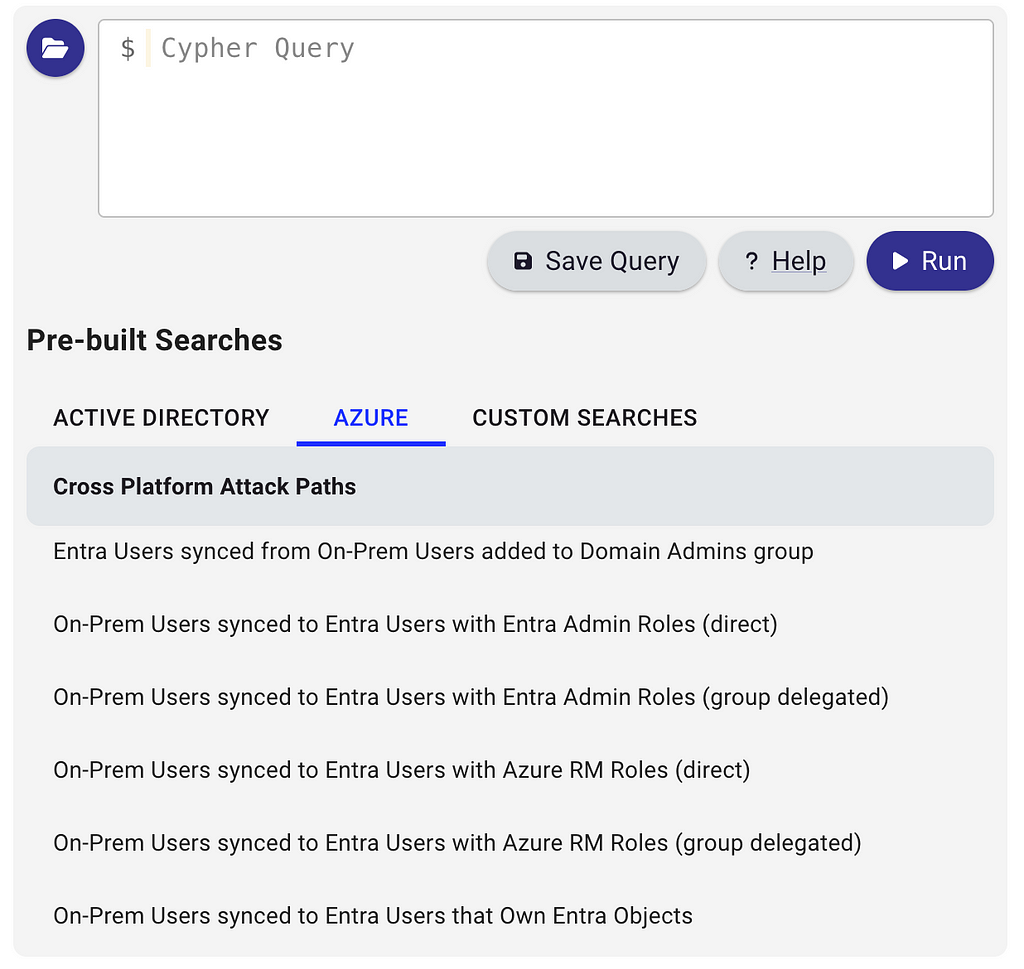
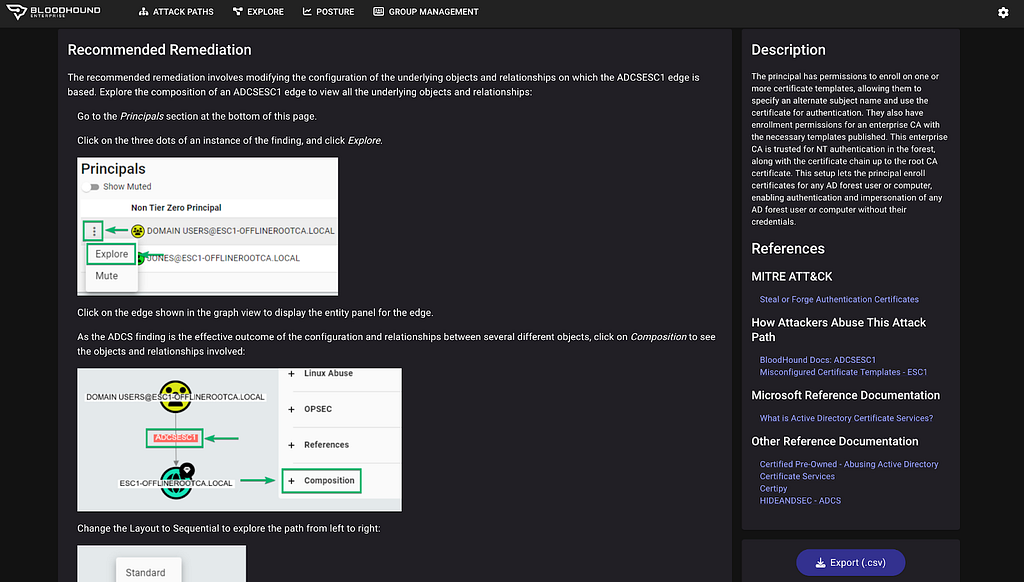
To support these changes, we’ve included several additional pre-built queries in BloodHound for potentially interesting paths for hybrid environments. After clicking on the “Open” folder on the Cypher tab, these queries are available underneath the Azure section:
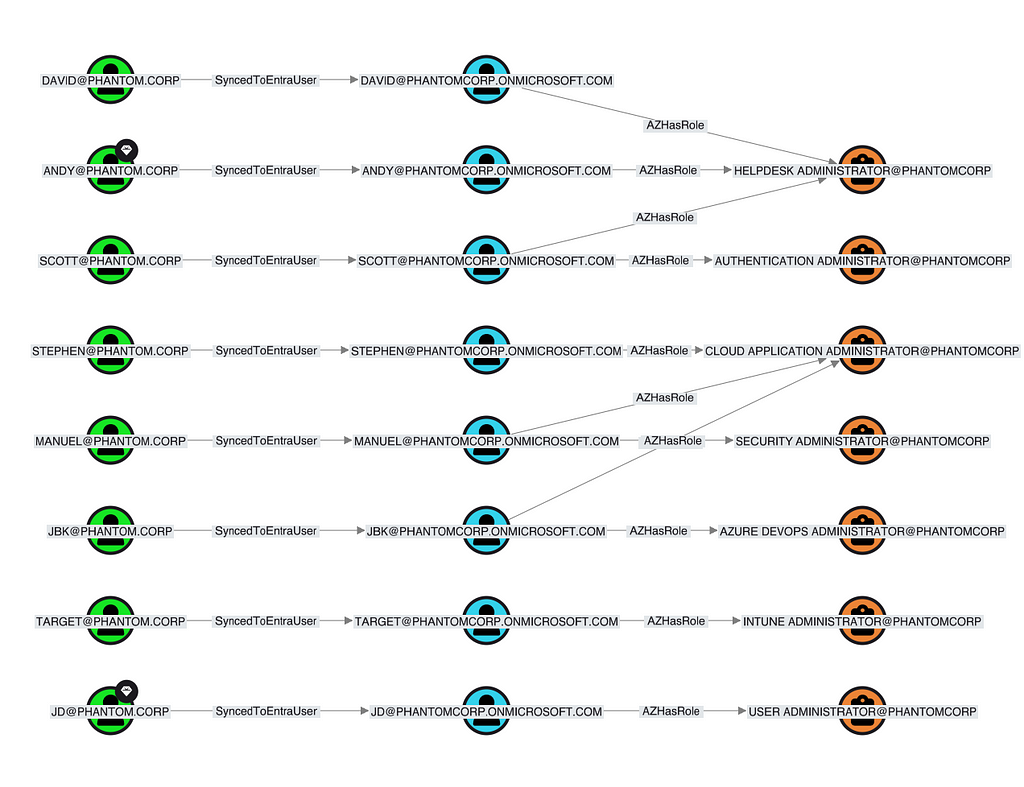
Here’s a set of results from our example dataset for the pre-built query named on-premises Users synced to Entra Users with Entra Admin Roles:
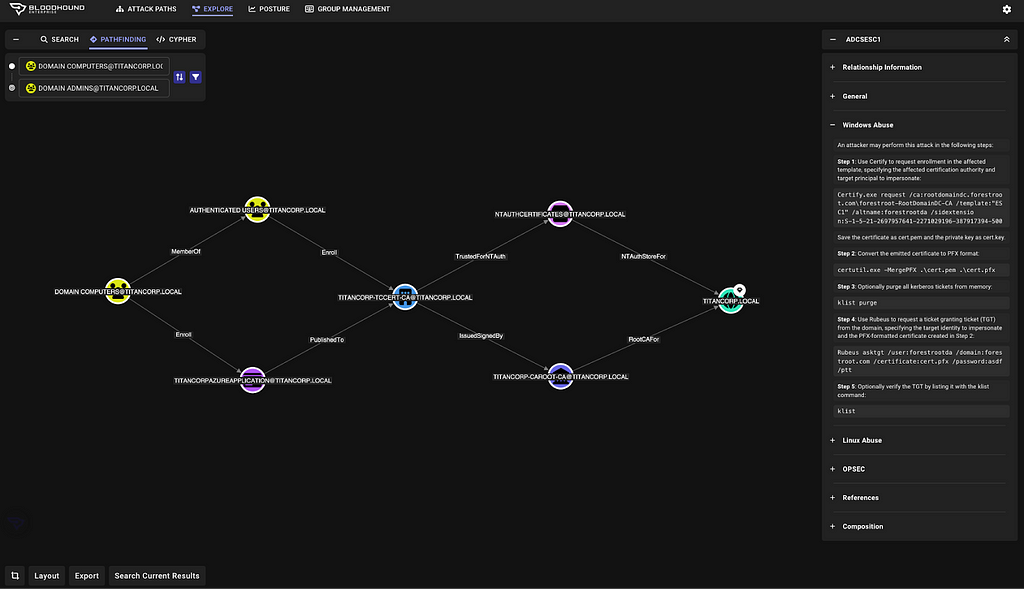
Pathfinding also supports Hybrid Paths, which can uncover those configurations that allow BloodHound to cross from on-prem AD to Azure or vice versa. Here, we show a path starting from anyone in the on-premises domain to Global Administrators in Entra via ADCS and synced user accounts:

We are very excited to introduce these new edges into the product for testing and validation of hybrid environments. We are already hard at work to research and introduce additional hybrid paths, including computer object synchronization. Additionally, we are developing a capability within BloodHound Enterprise that will enable us to empirically measure the risk to our customers’ critical Tier Zero assets across these hybrid paths. We look forward to sharing more with everyone soon!
BloodHound Enterprise Attack Paths View Improvements
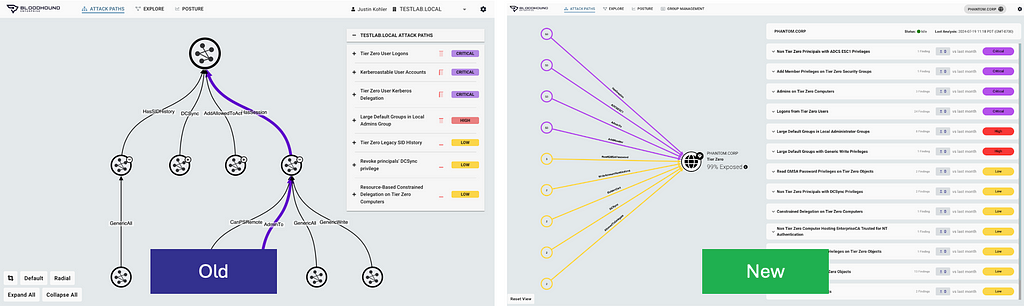
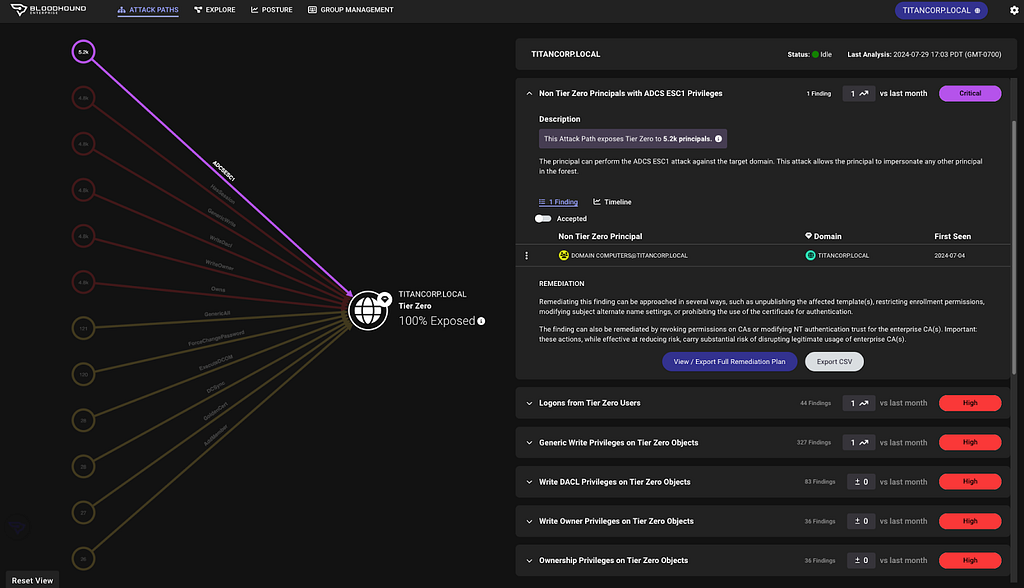
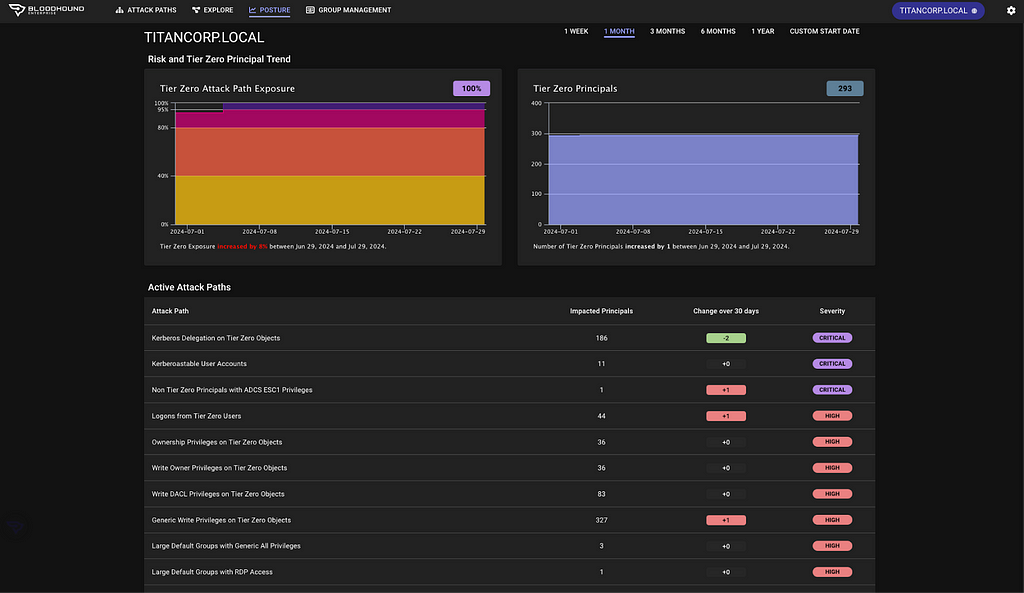
To kick off the start of the many UI improvements we have planned this year, we released an updated attack paths page for BloodHound Enterprise customers with increased readability and enhanced granularity:
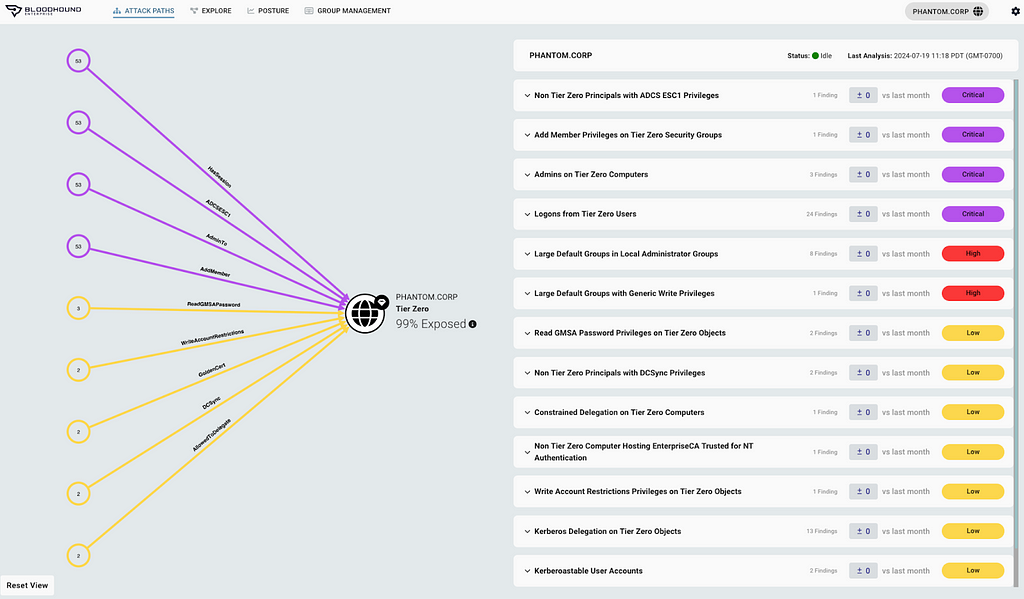
First, we re-oriented the attack graph to a more familiar left-to-right view versus top to bottom:
This layout now clearly identifies the Tier Zero / critical asset group and states the current exposure for the domain or tenant.
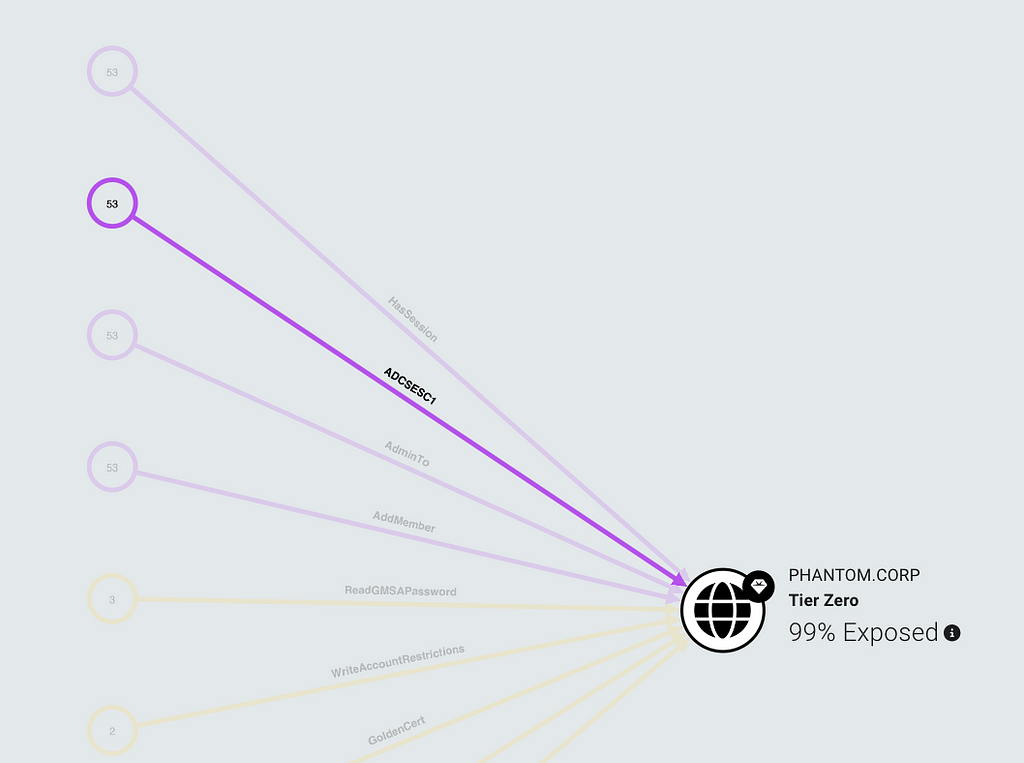
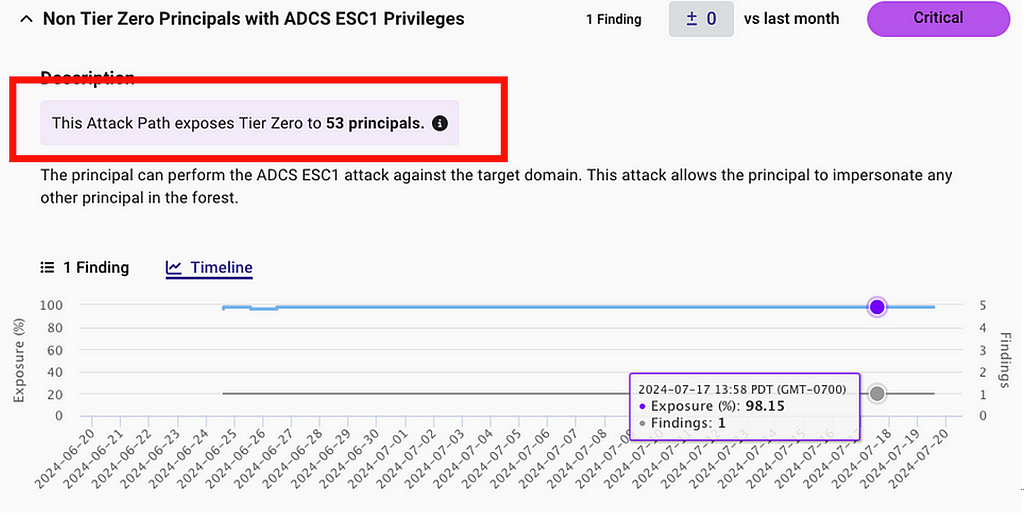
We are also introducing a new attribute in this view called “Exposed Principals”. BloodHound Enterprise has always calculated this value but has previously only represented it as a percentage; now this is directly stated as a numeric value in the Attack Path view for additional clarity:
Today in BloodHound Enterprise, Attack Paths are given a severity rating based on their exposure percentage to Tier Zero:
- Critical — 96%+ Exposure
- High — 81–95% Exposure
- Moderate — 41–80% Exposure
- Low — 0–40% Exposure
Now we can not only report the percentage of identities and resources that have an Attack Path, but also include the raw count. This is helpful in large domains where Exposure percentage could be low (30% for example) and the count is useful to still articulate that “This Attack Path exposes Tier Zero to 35,364 principals”.
This number is included in both the Attack Path detail and the graph:
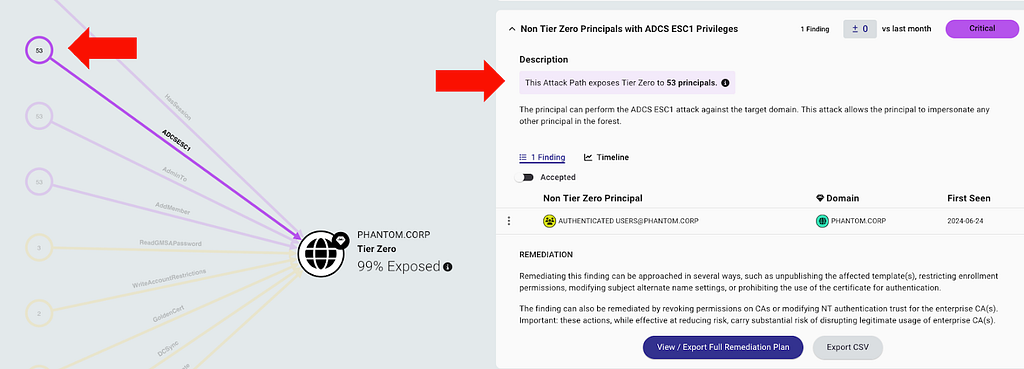
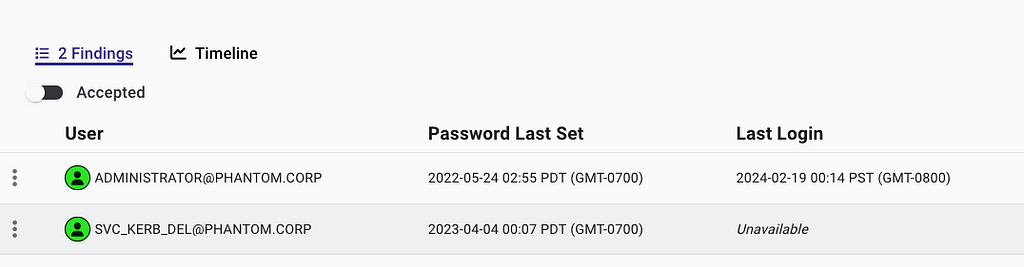
Next, we’ve included the count of findings within the header for every Attack Path:
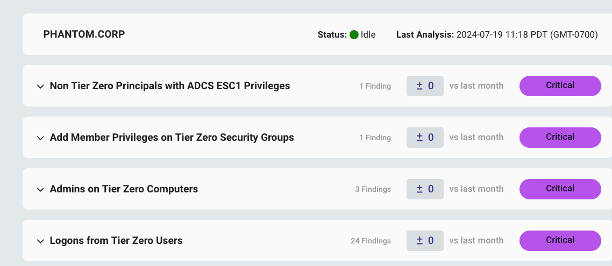
This allows our users to understand the level of effort to help them better prioritize where to start. In this case, we have two Attack Path choke points that can be completely remediated with less effort.
The Attack Path choke points have also been given more viewable space (50% versus 30%) to make it easier to read the details and we’ve also added a button to drop the results to CSV:
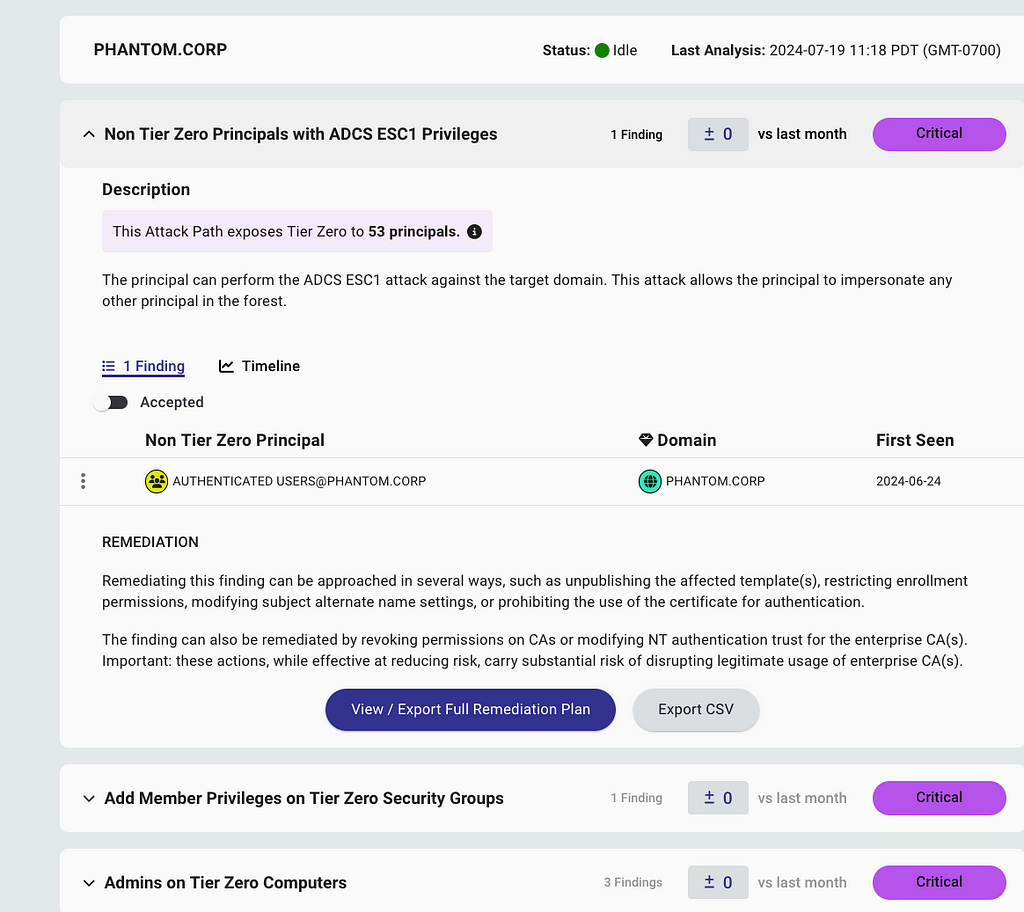
You’ll also notice new helpful columns have been added to the findings details based on the type of Attack Path. For example, we’ve included the age of the password in the “Kerberoastable Users” findings as an indication of which passwords maybe easier to crack:
Introducing Dark Mode for BloodHound
Dark mode is now in early access for both BloodHound Community Edition and BloodHound Enterprise:
Dark mode can be enabled / disabled through the settings cog on the upper right-hand side of the product (after enabling in Early Access):
For our Enterprise customers, this new theme applies to all portions of the product:
We also standardized our light theme across the product to be more consistent and set up the introduction of other themes in the future. Try it now to remove some of that eye strain and let us know your thoughts!
Going to BlackHat next week? Check out all the updates in person at our booth (#2600) or come hang out with us and a ton of other amazing industry folks at our bowling party on Wednesday evening: https://events.humanitix.com/specterops-black-hat-happy-hour-at-brooklyn-bowl
Hybrid Attack Paths, New Views and your favorite dog learns an old trick was originally published in Posts By SpecterOps Team Members on Medium, where people are continuing the conversation by highlighting and responding to this story.