introduction
New Follow-on Course to Adversary Tactics: Red Team Operations!
As modern architecture increasingly shifts services and data from on-premises infrastructure to the cloud, Identity becomes the thread that ties everything together.
Our Adversary Tactics: Identity-driven Offensive Tradecraft course is a follow-on to our Adversary Tactics: Red Team Operations course and offers an in-depth look at identity-driven attacks, targeting both on-premises and hybrid identities. Participants will learn how to abuse the intricacies of different authentication and authorization mechanisms to traverse on-premises and cloud environments, gain access to integrated systems, and even cross tenants. Participants will also be equipped with a practical approach to identifying known Attack Paths and forging new ones within complex operational environments and across people, processes, and technology.
course summary
Identity-driven Offensive Tradecraft
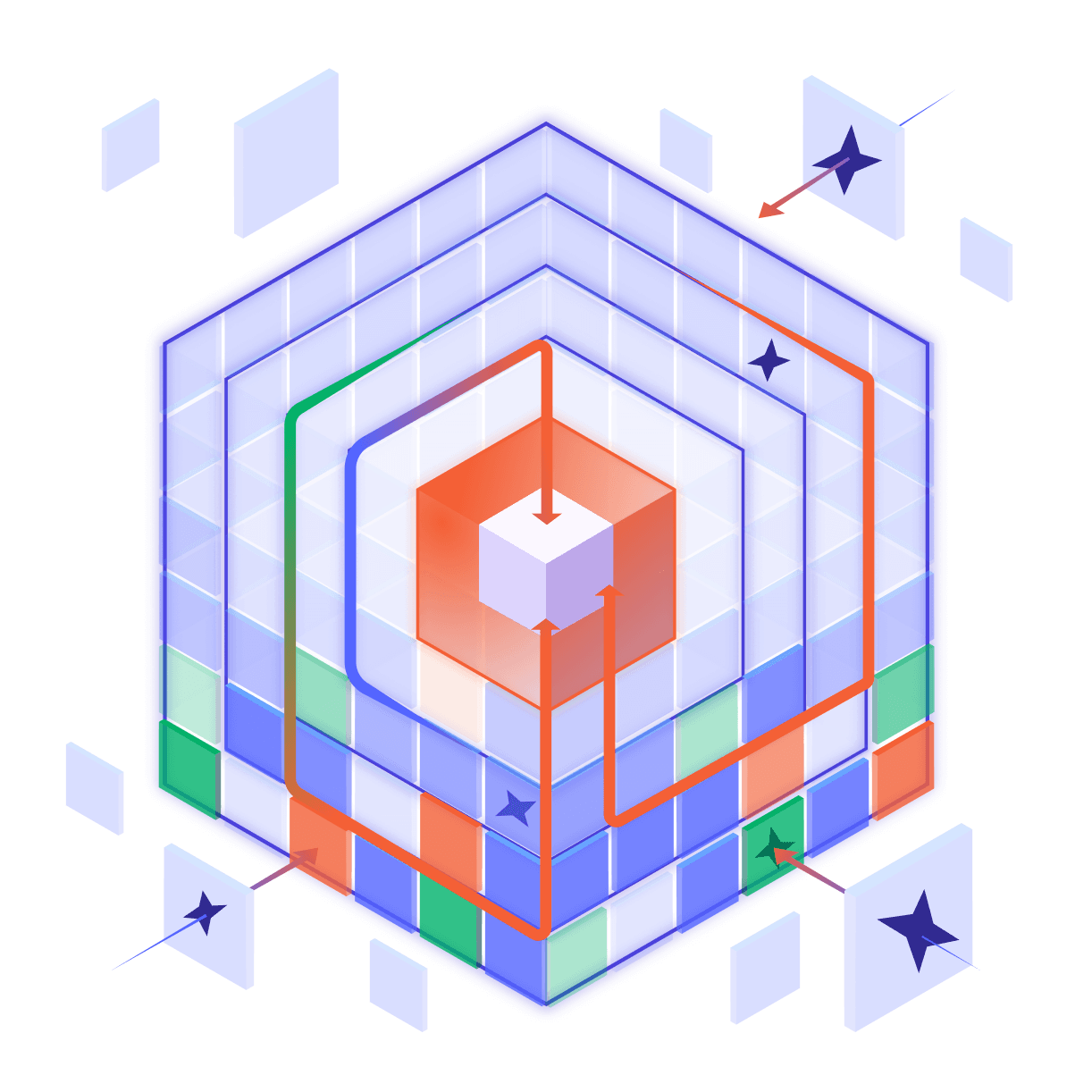
Modern ecosystems rely on Identity Providers (IdP) and Identity and Access Management (IAM) systems to authenticate users and govern access. Threat actors and red teams alike have been adopting and adapting “identity-driven” tradecraft to navigate modern environments and identity attack paths to their objectives. But what turns a path into an attack path? How do attackers discover new paths? And how do they abuse identity and access management platforms to execute attacks and impact the target?
Day 1
- Attack Path Identification Methodology
- Active Directory Situational Awareness
- Active Directory Guided Attacks
- Kerberos Delegation Abuse
- NTLM Tradecraft
- Authentication Coercion Techniques
Day 2
- Introduction to PKI, Active Directory Certificate Services, and PKINIT
- Certificate Abuse Techniques and Shadow Credentials
- Active Directory Federation Services, SSO, and SAML Attacks
Day 3
- Okta Deployment Scenarios
- Okta Abuse for Lateral Movement and Privilege Escalation
- SCCM Tradecraft and Hierarchy Takeover Techniques
Day 4
- Introduction to Entra ID and Azure Architecture
- OAuth and OpenID Flows in Entra ID
- Consent and Grant Flows
- Token Abuse
- Targeting Hybrid Environments
- Cross-Tenant and Supply Chain Attacks
Overview
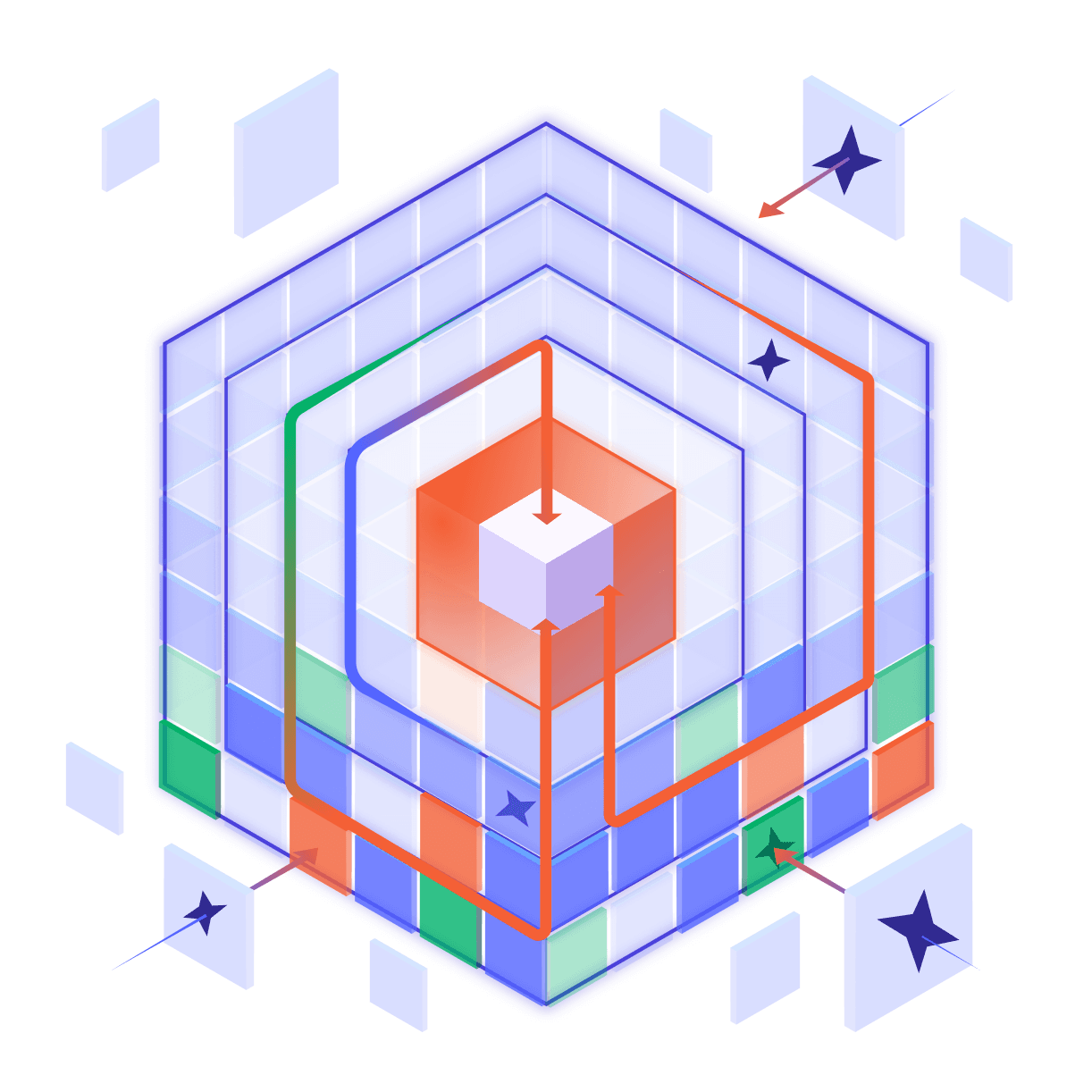
Adversary Tactics: Identity-driven Offensive Tradecraft equips participants with a method of discovering attack paths in complex environments, including previously disclosed techniques, as well as new attack primitives in common technology stacks and bespoke internal systems and processes. Participants will learn to identify and execute a wide range of elaborate attacks against both on-premises and cloud technologies. They will practice these skills hands-on in a specially designed lab environment that simulates a real-world client environment incorporating a variety of technologies and attack paths, including cross-tenant and supply chain attacks. Technologies covered include Kerberos, NTLM, ADCS, ADFS, SAML, Okta, Entra ID, OAuth, Azure, and hybrid identities.
In typical SpecterOps fashion, “Red vs. Blue” discussions are incorporated into the lectures to provide participants with the defender’s perspective and detection logic, as well as OPSEC considerations to counter those. A defender will also actively “hunt” participants in the lab to push them to improve their tradecraft by making educated decisions.
Training Participants
Who Should Take This Course
- Red teamers and penetration testers seeking to learn advanced tradecraft that works in mature environments.
- Blue teamers seeking to gain insight into advanced tradecraft commonly used by advanced threat actors.
- Security practitioners seeking to learn a methodic approach for identifying attack paths in complex systems or environments.