Unwrapping BloodHound v6.3 with Impact Analysis
Just in time for the holidays, sharper tools for faster defense Today, the SpecterOps team rolled out a number of new features, product enhancements, and recommendations intended to help users of BloodHound Enterprise and BloodHound Community Edition more easily visualize attack paths and show improvements in identity risk reduction over time. Scroll down to learn more […]
SPA is for Single-Page Abuse! – Using Single-Page Application Tokens to Enumerate Azure
Author: Lance B. Cain Overview Microsoft Azure is a leading cloud provider offering technology solutions to companies, governments, and other organizations around the globe. As such, many entitles have begun adopting Azure for their technology needs to include identity, authentication, storage, application management, and web services. One of the most common methods for organizations to begin […]
FedRAMP High Authorization for BloodHound Enterprise is a Critical Win for the Public Sector
Author: David McGuire, CEO, SpecterOps Today, we’re thrilled to announce that SpecterOps has earned FedRAMP High Authorization for BloodHound Enterprise! This is no small achievement, as it makes our BloodHound Enterprise identity security platform available to U.S. government organizations that operate at the FedRAMP High baseline. This shows SpecterOps’ commitment to data security for all […]
Azure Key Vault Tradecraft with BARK
Brief This post details the existing and new functions in BARK that support adversarial tradecraft research relevant to the Azure Key Vault service. The latter part of the post shows an example of how a red team operator may use these commands during the course of an assessment. Authentication Azure Key Vault is one of […]
Maestro: Abusing Intune for Lateral Movement Over C2
If I have a command and control (C2) agent on an Intune admin’s workstation, I should just be able to use their privileges to execute a script or application on an Intune-enrolled device, right? Not so fast. I Wanna Go Fast! Take me to the GitHub repo! Take me to the attack path walkthrough! Take me to the defensive […]
BOFHound: AD CS Integration
TL;DR: BOFHound can now parse Active Directory Certificate Services (AD CS) objects, manually queried from LDAP, for review and attack path mapping within BloodHound Community Edition (BHCE). Background My last BOFHound-related post covered the support and usage strategies for Beacon object files (BOFs) enabling the manual collection of data required for BloodHound’s AdminTo and HasSession edges, […]
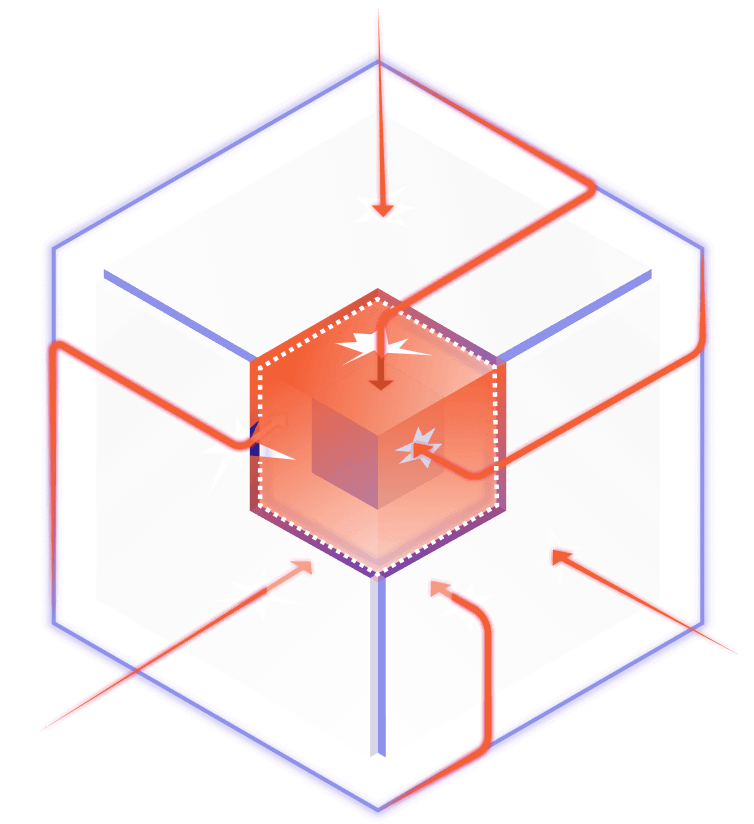
Closing the Gaps: How Attack Path Management Improves Vulnerability Management Programs
In conversation: Pete McKernan & Luke Luckett As organizations seek to wrap their arms around potential cybersecurity exposures, CIOs and CISOs are increasingly pushing their vulnerability management teams to widen scope. With such a focus, the growing concept of continuous threat exposure management (CTEM) aims to prioritize whatever most threatens the enterprise, whether or not such […]
Dotnet Source Generators in 2024 Part 1: Getting Started
Introduction In this blog post, we will cover the basics of a source generator, the major types involved, some common issues you might encounter, how to properly log those issues, and how to fix them. Source Generators have existed since .NET 5 was first introduced in late 2020. They have seen numerous improvements since that initial release, […]
Ghostwriter v4.3: SSO, JSON Fields, and Reporting with BloodHound
Ghostwriter v4.3 is available now, and it enhances features introduced in previous versions of v4 in some exciting ways! In particular, this article will dive into how you can integrate a tool like BloodHound Community Edition (BHCE) with Ghostwriter v4.3. First, we would be remiss if we did not mention the refreshed single sign-on (SSO) feature. […]
ADCS Attack Paths in BloodHound — Part 3
ADCS Attack Paths in BloodHound — Part 3 In Part 1 of this series, we explained how we incorporated Active Directory Certificate Services (ADCS) objects into BloodHound and demonstrated how to effectively use BloodHound to identify attack paths, including the ESC1 domain escalation technique. Part 2 covered the Golden Certificates and the ESC3 techniques. In this blog post, […]