Conference: April 13-14, 2026 | Training: April 15-18, 2026
SO-CON 2026
Know Your Adversary
Where the community comes together to advance the practice of Attack Path Management

Where Identity Security Meets Community
What to Expect at SO-CON
SO-CON is the only conference dedicated to identity-based security and attack path management. The week begins with a two-day main conference packed with talks, research, and community exchange, followed by four days of deep-dive, hands-on trainings led by adversary-experienced practitioners.

Discover
Explore the newest methods, tools, and research for identity-based attack paths.

Learn
Deepen your understanding of adversary tradecraft with cutting-edge talks and hands-on sessions.

Meet
Connect with fellow industry professionals throughout an immersive week of learning.

FEATURED KEYNOTE
Kevin Mandia
Founder and Former CEO of Mandiant, Founder and CEO at Armadin & Co-Founder & General Partner at Ballistic Ventures
Kevin is one of the most respected leaders in cybersecurity, known for guiding organizations through major breaches and shaping how the industry understands modern adversaries.
His keynote will focus on how the threat landscape has evolved in the face of modern adversary tradecraft and what leaders should prioritize to strengthen their security posture.
TRAININGS
Level up your expertise with one of our four cutting-edge courses
- Free conference pass included
- Engage with our frontline practitioners
- Evening social events
Tradecraft Analysis
In Adversary Tactics: Tradecraft Analysis, we will present and apply a general tradecraft analysis methodology for offensive TTPs, focused on Windows components. We will discuss Windows attack techniques and learn to deconstruct how they work underneath the hood. For various techniques, we will identify the layers of telemetry sources and learn to understand potential detection choke points. Finally, the course will culminate with students creating their own technique evasion and detection strategy. You will be able to use the knowledge gained to both use your telemetry to create robust detection coverage across your organization, and truly assess the efficacy of that coverage.
Red Team Operations
This Red Team Operations course immerses students in a single simulated enterprise environment, with multiple networks, hardened endpoints, modern defenses, and active network defenders responding to red team activities. We will focus on in-depth attacker tradecraft post-initial access; braking out of the beachhead, establishing resilient command and control (C2) infrastructure, gain situational awareness through opsec aware host and network enumerations, perform advanced lateral movement and sophisticated Active Directory escalation, gain persistence (userland, elevated, and domain flavors), and perform advanced Kerberos attacks, data mining, and exfiltration.
Identity-driven Offensive Tradecraft
Identity-driven Offensive Tradecraft offers an in-depth look at identity-driven attacks, targeting both on-premises and hybrid identities. Participants will learn how to abuse the intricacies of different authentication and authorization mechanisms to traverse on-premises and cloud environments, gain access to integrated systems, and even cross tenants. Participants will also be equipped with a practical approach to identifying known attack paths and forging new ones within complex operational environments and across people, processes, and technology.
Detection
This Detection course builds on standard network defense and incident response (which often focuses on alerting for known malware signatures) by focusing on abnormal behaviors and the use of adversary Tactics, Techniques, and Procedures (TTPs). We will teach you how to engineer detections, steering clear of brittle indicators in favor of attacker TTPs. In addition, you will learn use utilize free and/or open source data collection and analysis tools (such as Sysmon, Windows Event Logs, and ELK) to analyze large amounts of host information and build detections for malicious activity.
Conference tracks
1
Tradecraft
Breaking and detecting real adversary behavior through cutting-edge offensive and defensive tradecraft.
2
OpenGraph
Advancing Attack Path Management through deep research on identity graphs, hybrid attack paths, and emerging threats.
3
Practice
Turning Attack Path Management into action with proven frameworks and real-world case studies.
TESTIMONIALS
Hear What Others Have to Say About SO-CON
Over the course of a week, SO-CON 2025 featured insightful talks and comprehensive training courses designed to deliver maximum value to all attendees. Hear from our guests as they share their experiences and insights in these video testimonials.
Conference Highlights
Questions? Email socon@specterops.io
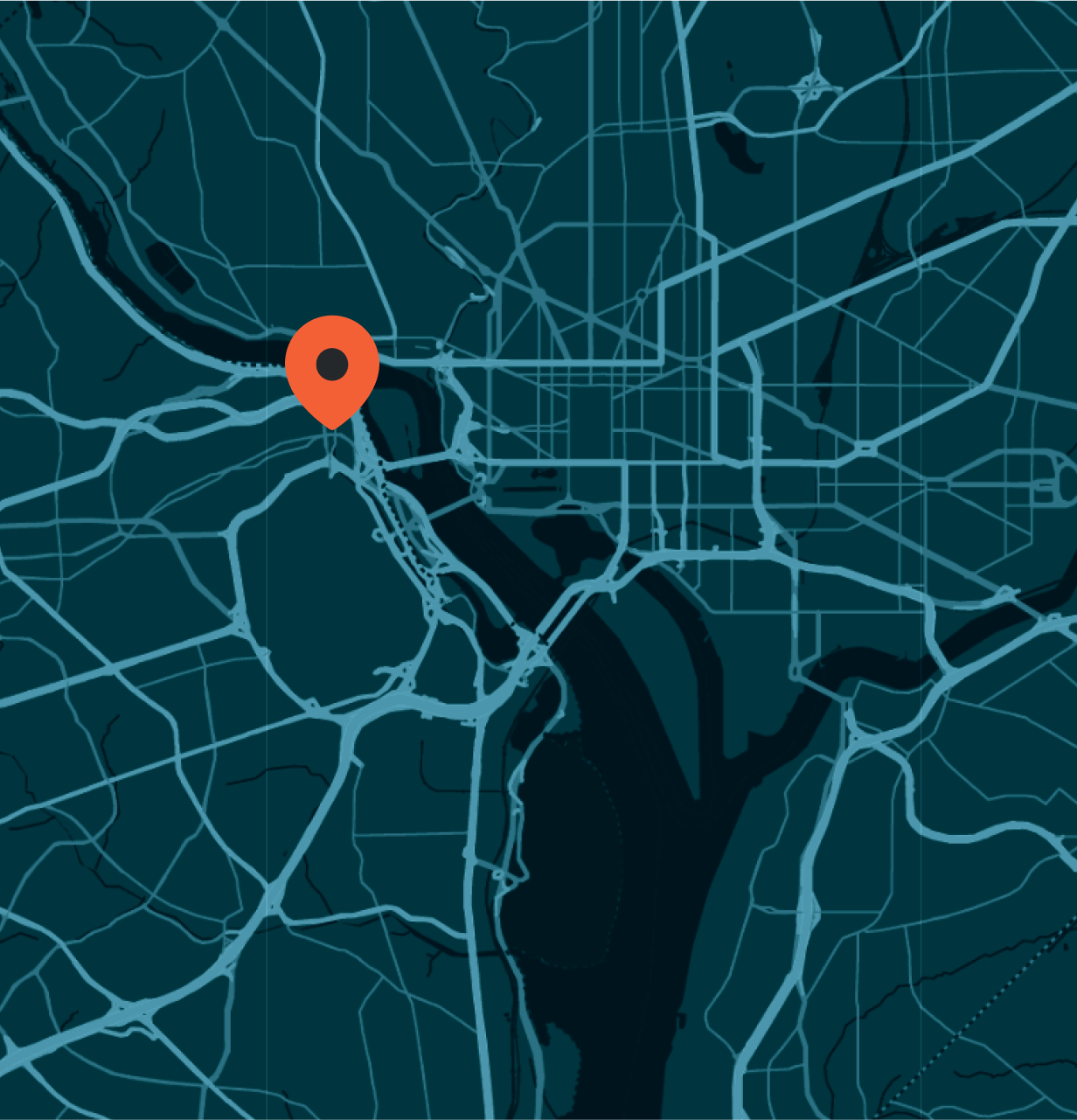
Event Location & Lodging
Location: Convene
1201 Wilson Blvd. Arlington, VA 22209
Hotels Nearby
Looking for a place to stay near the conference? These two hotels are just a short walk from Convene at 1201 Wilson Blvd, Arlington, VA.
Please note: We do not have room blocks available at these hotels.
Le Méridien Arlington
1121 19th Street North
Arlington, VA 22209
Hyatt Centric Arlington
1325 Wilson Boulevard,
Arlington, VA 22209
SO-CON 2026
Live in Convene | April 13 – 14, 2026