Tag
BloodHound
BloodHound
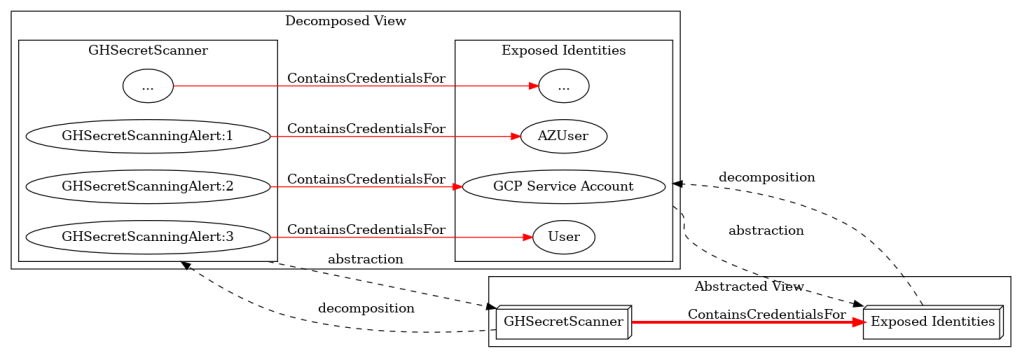
Taming the Attack Graph: A Many Subgraphs Approach to Attack Path Analysis
TL;DR This blog presents a framework using technology subgraphs, decomposition, and graph abstraction to model hybrid...
Nov 13, 2025
Read Post
BloodHound
AdminSDHolder: Misconceptions, Misconfigurations, and Myths
TL;DR: This blog is the brief version. I love delving into ancient history. The Fall of...
Oct 31, 2025
Read Post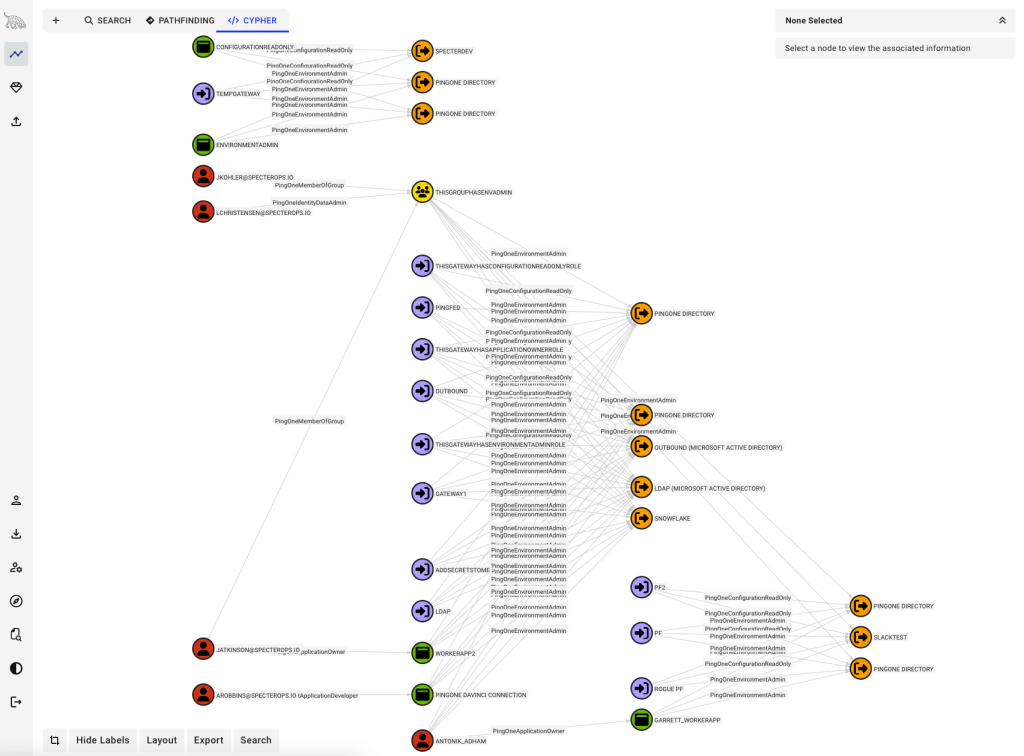
BloodHound
TL;DR: You can use PingOneHound in conjunction with BloodHound Community Edition to discover, analyze, execute, and...
Oct 20, 2025
Read Post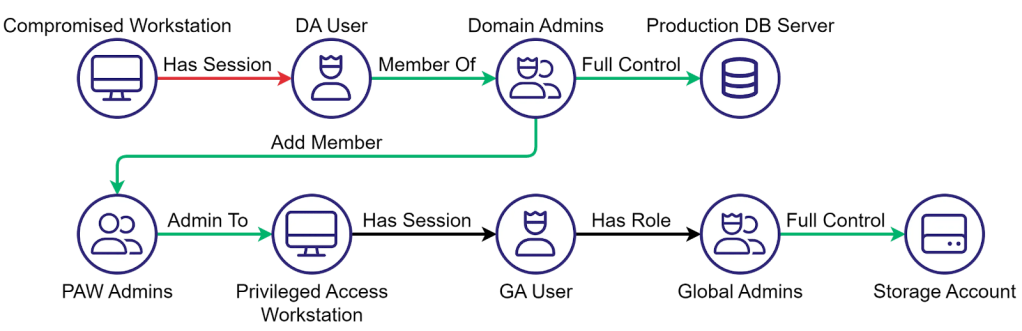
BloodHound
The Clean Source Principle and the Future of Identity Security
TL;DR Modern identity systems are deeply interconnected, and every weak dependency creates an attack path — no...
Oct 8, 2025
Read Post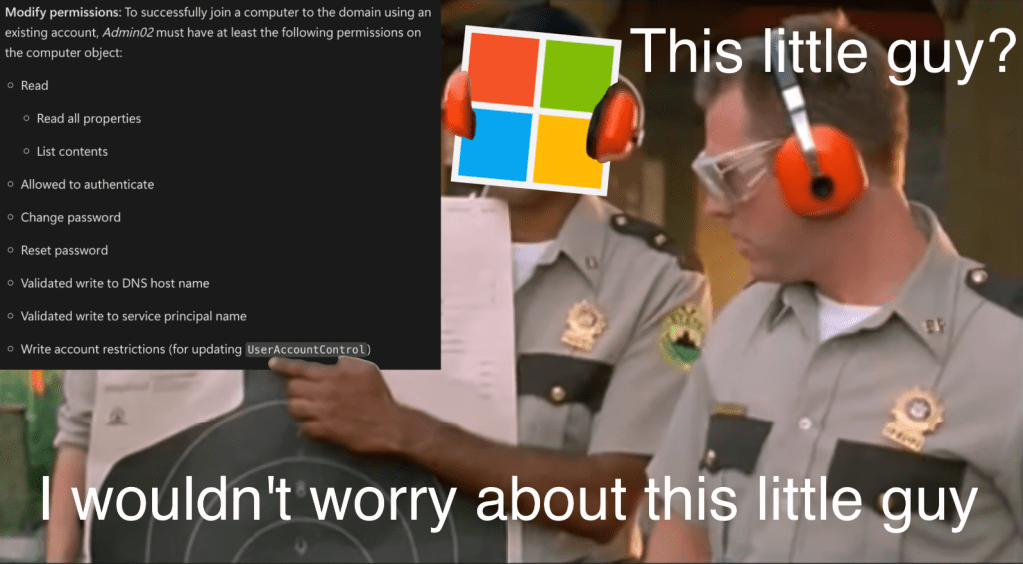
BloodHound
WriteAccountRestrictions (WAR) – What is it good for?
TL;DR A lot of things. The User-Account-Restrictions property grants read/write permissions to the user-account-control LDAP attribute,...
Oct 1, 2025
Read Post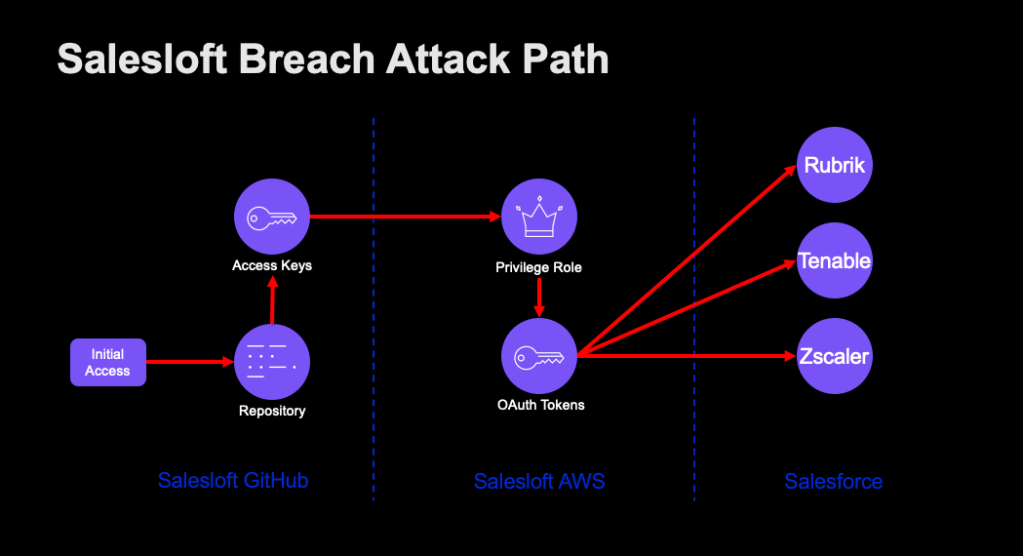
BloodHound
The Salesloft–Drift Breach: An Attack Path Case Study
TL;DR This post analyzes the Salesloft–Drift incident through an attack path lens, showing how violations of...
Sep 24, 2025
Read Post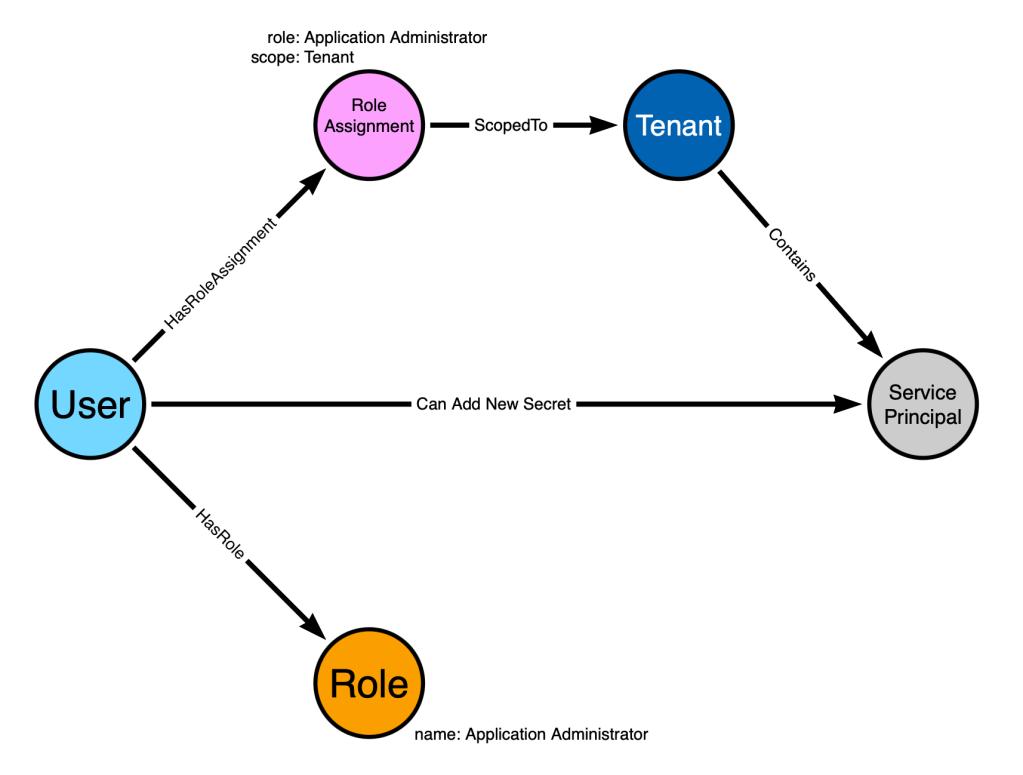
BloodHound
Attack Graph Model Design Requirements and Examples
TL;DR OpenGraph makes it easy to add new nodes and edges into BloodHound, but doesn’t design...
Aug 1, 2025
Read Post
BloodHound
Privilege Zones: BloodHound Enterprise spreading like a computer virus (of security)
TL;DR The BloodHound Enterprise team recently pushed out Privilege Zones, one of the most requested features...
Jul 8, 2025
Read Post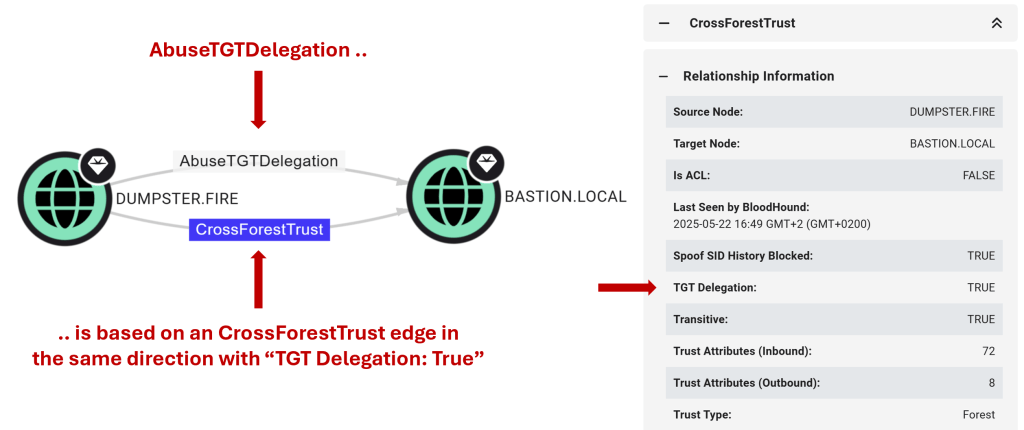
BloodHound
Good Fences Make Good Neighbors: New AD Trusts Attack Paths in BloodHound
TL;DR The ability of an attacker controlling one domain to compromise another through an Active Directory...