Getting the Most Value Out of the OSCP: The PEN-200 Labs
TL;DR How to leverage the PEN-200 simulated black-box penetration testing scenarios for maximal self-improvement and career success.
DISCLAIMER:
All opinions expressed in this article are solely my own. I have reviewed the content to ensure compliance with OffSec’s copyright policies and agreements. I have not been sponsored or incentivized in any way to recommend or oppose any resources mentioned in this article.
Introduction
In the last post of this series, I explored some hidden benefits and extra steps students should take when writing notes for the PEN-200: Penetration Testing with Kali Linux course. Before attempting the Offensive Security Certified Professional (OSCP) exam, it’s highly recommended to complete the practical lab networks. But first, read this article to learn how to maximize the lab experience.
Get your OSCP+ certification with PEN-200 | OffSec
PEN-200 is OffSec's foundational pentesting course– learn and practice the latest techniques. Earn your penetration testing certification (OSCP & OSCP+).
www.offsec.com

During the Labs…

“Success is no accident. It is hard work, perseverance, learning, studying, sacrifice, and most of all, love of what you are doing.” — Pelé
The PEN-200 course includes multiple virtual lab environments, each offering an opportunity to grow as an offensive security professional. The three key takeaways from this post are:
- Learn how to write a high-quality penetration testing report and apply those skills to each lab network
- Use the labs as a baseline to build your own testing environment where you can refine offensive techniques, understand how misconfigurations arise, and analyze network packets associated with different attacks
- Develop a repeatable testing methodology, apply it to the labs, and continuously refine it through an iterative process
Write Reports for Each Lab
For all the effort OSCP candidates put into identifying and exploiting technical vulnerabilities, the irony of the course is that its arguably most valuable skill is also the least offensive: report writing. In the real world, the value of an offensive security engagement doesn’t come from hacking efforts alone — it mostly comes from a legible, actionable, and informative report. Given this, it’s somewhat disappointing that the OSCP exam report — a required component of the certification process — is graded more on accuracy than quality. According to the PEN-200 Reporting Requirements, “[students] must submit an exam penetration test report clearly demonstrating how [they] successfully achieved the certification exam objectives”. This policy ensures that passing students have demonstrated the minimum technical competency of an offensive security professional, but not necessarily the writing skills needed to excel in the field. If your goal is not just to pass the exam but to be a standout candidate in future consulting roles, you should learn how to write an exemplary penetration test report and use the PEN-200 labs as practice.
Report writing is often the least enjoyable part of a penetration test, but a poorly written report can have serious consequences. The most immediate impact may be frustration from supervisors or colleagues, but the affected audience is often much larger. If your firm has a quality assurance (QA) process, multiple rounds of revision can delay the report’s delivery, damaging the company’s reputation. Worse, if significant errors slip through and the client receives a flawed report — such as one containing incorrect, incomplete, or difficult-to-read sections — the aftermath can be disastrous. Miscommunication about findings can lead to delayed security improvements, inadequate risk mitigations, and ultimately an unresolved attack surface. The client may become furious over wasted time and resources, potentially demanding revisions, reattempts, or — worst-case scenario — a partial or full refund.

Given the stakes, it’s imperative to take reporting seriously — and this is where the PEN-200 labs come in. While their official purpose is to provide students a sandbox environment for practicing their newly learned offensive techniques, they also serve as an excellent training ground for report writing. The lab structures simulate a black-box penetration test scenario, lending authenticity and relevance to aspiring offensive security professionals. Furthermore, three lab networks are specifically designed to replicate the OSCP exam conditions, allowing students to simulate the exam environment under self-imposed time constraints.
NOTE:
Consider attempting two of these lab networks within a 48-hour window (24-hours each for testing and reporting) before your first exam attempt, reserving the third for after you’ve conducted your first attempt postmortem (more on that later in the series).
Before you begin report writing, it’s essential to understand their structure. While formats vary across firms, most reports include at least an Executive Summary, Assessment Results, Attack Path Narrative, and Appendix. A full breakdown of these sections is beyond the scope of this post, but for practical guidance, Brian King’s Hack for Show, Report for Dough (Wild West Hackin’ Fest 2018) is a phenomenal resource. It also covers several report writing best and worst practices, helping students refine their skills. Students can also reference OffSec’s official OSCP exam report templates as a primary source for understanding the certification provider’s expectations.
When writing reports, I strongly advise sticking to Microsoft Word. While I personally find it somewhat infuriating and a victim of “featuritis”, it remains the dominant word processor application in the industry and offers useful features like change trackers (especially relevant for collaborative projects), cross-references, and a citation management system. For screenshots, I highly recommend Greenshot, Flameshot, Snagit, and ZoomIt from the Sysinternals suite. Including a network topology diagram in your lab reports can improve clarity — draw.io is a popular choice for this. Finally, ensure that your report writing toolset does not violate OffSec’s Academic Policy; for example, as stated in the OSCP Exam Guide, using large language models (LLMs) and artificial intelligence (AI) chatbots to generate or refine content constitutes sharing PEN-200 material with a third-party, which is a copyright violation.
Each firm has its own style guide for consultants, so it’s important to adopt a writing style that aligns with industry expectations when creating lab reports. While I couldn’t find a publicly available style guide specifically for penetration test reports, the Microsoft Writing Style Guide serves as a suitable alternative. Below are key writing principles to follow, with some modifications and additions to Microsoft’s guide:
- Use active voice over passive voice (e.g., “the student scanned the host…” vs. “the host was scanned by the student…”), unless the latter sounds objectively less “awkward”
- Maintain a consistent preterite verb tense and third-person narrative (e.g., “the student conducted a penetration test…”)
- Spell out acronyms on first use (e.g., “dynamic link library (DLL)”)
- Ensure text in screenshots is at least as large as figure subtitles or body text for readability
- Avoid opinionated language, colloquialisms, redundant phrases, and contractions to maintain a professional tone
Welcome – Microsoft Writing Style Guide
The online Microsoft Writing Style Guide provides up-to-date style and terminology guidelines. It replaces the Microsoft Manual of Style.
learn.microsoft.com

The main drawback of using the PEN-200 labs for report writing practice is that students cannot share their reports for peer-review due to copyright restrictions. According to Section 16 (IP Ownership) of OffSec Terms and Conditions, students are forbidden from sharing derivative PEN-200 content such as lab walk-throughs — which implicitly includes reports. Violating this agreement could result in punitive action from OffSec, such as having existing certifications revoked or being banned from future enrollment. To work within these constraints, students should conduct independent research on report writing and rigorously self-grade their reports while keeping them private. Those seeking peer feedback can instead write reports on alternative virtual lab environments with looser copyright restrictions, such as Hack the Box (HTB), and request evaluation from qualified career mentors.
It’s in your best interest to start developing your report writing skills early and the professionally managed PEN-200 lab networks provide an excellent environment to practice within. If you’re still struggling with report writing — or want to learn more about report review, delivery, and feedback procedures in general — consider enrolling in Luke Rogerson’s The Art of Report Writing, offered by Zero-Point Security. While I haven’t personally taken the course, it comes highly recommended by many in the consulting field and features an expansive syllabus. Investing in your report writing abilities — both during the PEN-200 labs and through external resources — will pay dividends in your future career.
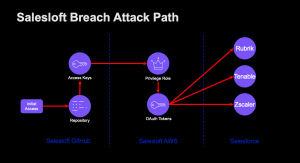
Use the Labs as a Baseline for Your Personal Lab
The PEN-200 labs are excellent for simulating black-box penetration tests, but students shouldn’t rely solely on them for experimenting with offensive techniques. Your ultimate goal should be to either design a personal lab for yourself or use an existing template by the time you have completed the PEN-200 labs. If you choose to follow the former path, don’t be afraid to take inspiration from the labs when designing your own.

Developing your own cyber range offers several advantages over the PEN-200 labs. Most obviously, your lab access won’t expire when your OffSec subscription ends. Setting up a personal lab manually also deepens your understanding of how misconfigurations and vulnerable applications introduce security risks. You can also expand upon the PEN-200 syllabus by incorporating technologies not covered in the course, such as security incident and event management (SIEM) solutions, Kerberos delegation attack paths, and persistence techniques, to name a few. If you want to get even more granular, you can use a network protocol analyzer utility like Wireshark to manually inspect the network packets associated with your favorite tools or exploits. Finally, for students eager to stay current with cybersecurity trends, a personal lab provides a low-risk environment to deploy and test new exploits and tools.
Historically, deploying a personal cybersecurity lab was a costly endeavor. The resources required to simulate an entire Active Directory (AD) network required substantial investments in RAM, CPU cores, and HDD/SSD storage, often housed in bulky rack servers or large PC chassis. For those starting from scratch, costs can easily creep up to hundreds or even thousands of dollars. Luckily, mini PCs like the GMKtec NucBox offer a significantly more affordable and compact alternative to the comically large and expensive gaming rigs often associated with home labs. You can even purchase a barebones mini PC — no RAM, SSD, or OS pre-installed — and salvage memory and storage components from refurbished PCs. By integrating them into a custom-built setup and installing an open-source OS like Ubuntu, you can significantly cut costs while still aggregating the hardware required to create a fully functional lab environment.
Deploying a cybersecurity lab has traditionally been seen as a technically demanding experience due to the sheer scope of involved technologies. Most PEN-200 students may already be familiar with virtualization platforms like VMware Fusion and Workstation or Oracle VirtualBox, but not necessarily infrastructure as code (IaC) tools like Vagrant, Terraform, Ansible, and Packer. Similarly, containerization platforms such as Docker, Podman, or Kubernetes (K8s) introduce additional complexity. Once the lab is deployed, students must also administer network segmentation, domain name system (DNS) records, snapshot management, and, in the case of free licensed Windows virtual machines (VMs), manually extend the 180-day trial period by rearming the instance. Thankfully, platforms like Ludus have emerged to simplify the cybersecurity lab deployment process, consolidating many of these technologies into a single, streamlined solution.
Ludus is a cyber range orchestration platform that Erik Hunstad, the founder of Bad Sector Labs and Chief Technology Officer of Sixgen, created. The platform is built on top of the Proxmox Virtual Environment (Proxmox VE) hypervisor — a powerful open-source solution for VM and container management — enabling the virtualization of entire simulated networks. Among its many features, Ludus supports user-defined networking and firewall rules, DNS record management, snapshot functionality, and automated configuration pulls from Ansible Galaxy’s collection library. It deploys VM templates that can either be sourced from Ludus’s builtin library or customized and imported. The end-user only needs to install Ludus on a dedicated host, create an environment configuration file, deploy the range, and apply host- or domain-specific changes — which can easily be automated. Ludus is an extremely powerful and customizable tool for students who want to focus on refining their penetration testing skills rather than spending excessive time troubleshooting setup issues.
server_cluster
docs.ludus.cloud
Designing a cyber range from scratch can be intimidating, but fortunately, multiple preconfigured penetration testing labs are available for students to deploy. One of the most popular lab templates today is Game of Active Directory (GOAD) by M4yFly, offered by Orange Cyberdefense. GOAD supports multiple attack path scenarios, many of which are covered in the PEN-200 course, making it an ideal choice for a first personal cyber range. It is also compatible with Ludus, further simplifying deployment.
Game Of Active Directory v2
Yes another pentester blog..
mayfly277.github.io
Regardless of whether you use GOAD, a custom-built network, or another public lab template, consider supplementing the range with Elastic Security, an SIEM platform from the Elastic Stack (ELK). Integrating Elastic Security — or another free SIEM solution — into your lab allows students to observe how offensive techniques are detected in real time, providing valuable insights into defensive strategies. Elastic Security is also Ludus-compatible and, to demonstrate how to integrate it with a personal cyber range, I recommend this walkthrough from I.T. Security Labs that shows how to deploy GOAD with Elastic Security through Ludus.
NOTE:
Other noteworthy lab templates include BadBlood, ADCS Lab, and SCCM Lab, the last two of which are compatible with Ludus. BadBlood (by Secframe) is a PowerShell scripting suite that generates polymorphic Microsoft AD cyber ranges, ensuring distinct challenges with each invocation. The ADCS and SCCM labs focus on Active Directory Certificate Services (AD CS) and Microsoft Configuration Manager (MCM/SCCM). While not covered in the PEN-200 syllabus, recent security research has demonstrated that they both represent a significantly large attack surface, and the aforementioned labs provide an opportunity to develop skills in testing and securing both technology stacks.
In conclusion, a personal cybersecurity range inspired by the PEN-200 lab networks provides several key advantages: freedom from OffSec subscription limits, exposure to multiple relevant technologies, a sandbox for testing new techniques and tools, and the ability to integrate operational security (OPSEC) solutions. If you successfully design a custom penetration testing lab from scratch (not derivative of PEN-200 content), you can share your deployment template publicly — a valuable addition to your portfolio that can strengthen future job applications.
Develop a Testing Methodology
Once you begin the PEN-200 labs, it’s crucial to develop a repeatable and self-improving testing methodology early to avoid falling into a “spray and pray” mentality. A structured approach not only helps you uncover hidden vulnerabilities more efficiently, but also minimizes the risk of needing lab extensions or incurring multiple exam retake fees — maximizing the value of your PEN-200 experience.
In the context of PEN-200 and offensive security, a testing methodology is a systematic process encompassing enumeration, documentation, tool selection, exploit testing, privilege escalation, and post-exploitation routines. Ideally, your methodology should evolve as you progress through the labs, allowing you to address knowledge gaps, adopt time-saving techniques, and incorporate novel attack strategies. Students who follow a codified and mature testing methodology are less likely to waste time redoing scans, chase dead ends, overlook low-hanging fruit, become prone to burnout and frustration, or rely on luck or accidental success to achieve the testing objective.

In the first post of this series, I introduced the concept of command reference guides (AKA “cheat sheets”), which serve as a repository for your preferred offensive tooling usage. Beyond providing easy copy-and-paste shortcuts for commands, your reference guide can be structured to align with your testing methodology. In our previous example, I demonstrated how you could leverage Obsidian to document the usage of impacket-GetUserSPNs for conducting a Kerberoasting attack. Let’s expand on this example by organizing the navigation pane of the guide into distinct phases of a simple penetration testing methodology.

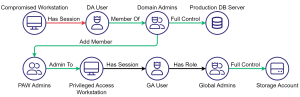
Our reference guide now consists of seven root directories, each representing a major phase of a typical penetration test (e.g., Reconnaissance, Initial Access, Privilege Escalation, etc.). Notice how each of the three tools we’ve added so far (i.e., impacket-GetUserSPNs, BloodHound, and Hashcat) is intuitively placed within the appropriate parent directory, and further compartmentalized into subdirectories based on the specific technique utilized during that phase (e.g., Identifying Kerberoastable Accounts, Kerberoasting, Hash Cracking, etc.). In the Internal Enumeration and Privilege Escalation phases, we’ve gone a step further by dividing techniques by the environment we’re working in — in this case, Active Directory, Linux, and Windows. Since Kerberoasting is specific to AD environments, we placed our entry for BloodHound and impacket-GetUserSPNs in the Active Directory subdirectory of Internal Enumeration and Privilege Escalation, respectively.
I want to emphasize the importance of iterative learning when developing your testing methodology. It’s unrealistic to expect that your initial attempt at following a testing methodology will be optimal, so it’s critical to refine your process after each lab or exercise — especially during the early, high-growth stage of your OSCP journey. Consider keeping a brief log for each machine or network within your reference guide, summarizing the attack path, the tools and techniques you utilized, and the areas where you struggled most. Use the last section in particular to feed both successes and setbacks into your methodology refinement. This continuous improvement process will steadily strengthen your assessment methodology, significantly boosting your confidence and skills ahead of the OSCP exam.
In conclusion, I strongly encourage students to treat the labs not just as an opportunity to improve their ability to identify and exploit vulnerabilities, but also as a chance to build an iterative, professional methodology for offensive security engagements — and to commit to regularly polishing it as they progress. Doing so will not only prepare you for the OSCP exam, but will also translate directly to future responsibilities in a consulting role, strengthen your technical interview performance, and ultimately support your growth as a security professional.
Conclusion

If you have questions, feedback, or suggestions you feel should have been included in this post, please feel free to leave a comment. In the next installment of this series, I’ll dive into the OSCP exam itself.
Getting the Most Value Out of the OSCP: The PEN-200 Labs was originally published in Posts By SpecterOps Team Members on Medium, where people are continuing the conversation by highlighting and responding to this story.