blog category
Research & Tradecraft
Research & Tradecraft
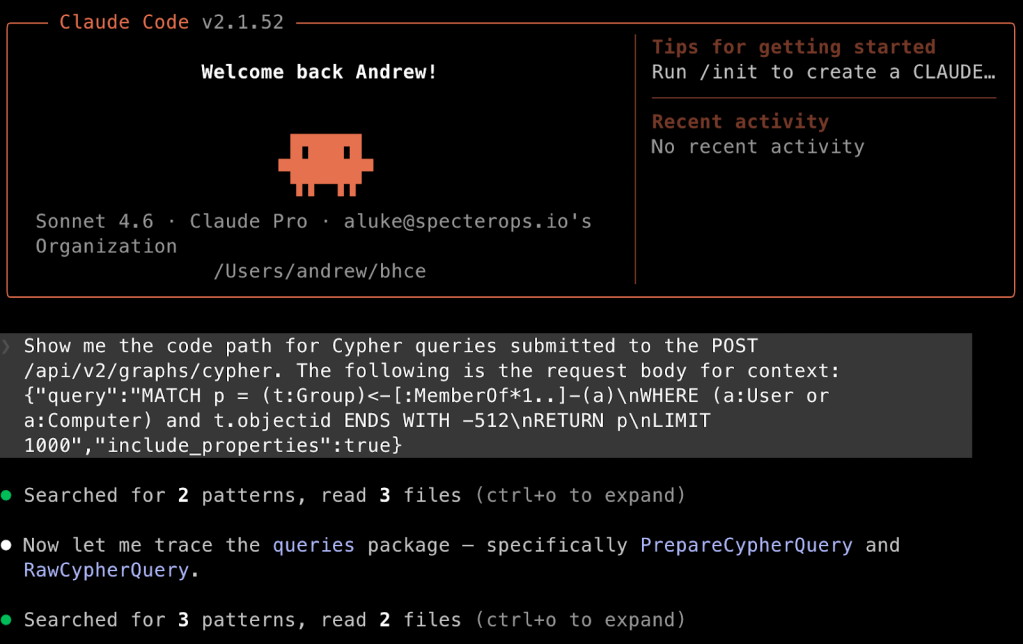
Leveling Up Secure Code Reviews with Claude Code
TL;DR: Claude Code is a force multiplier when performing secure code reviews during an assessment. In...
By: Andrew Luke
Mar 26, 2026 • 18 min read
Read Post
Research & Tradecraft
Attack Paths Don’t Stop at Identity Providers
Modeling Okta in BloodHound Enterprise to uncover cross-platform identity risk Introduction Identity is no longer confined...
By: Jared Atkinson
Mar 24, 2026 • 10 min read
Read Post
Research & Tradecraft
RTFM: Read The Fatal Manual – When Vendor Documentation Creates Critical Attack Paths
TL;DR: Trusted vendor documentation across 16 major technology companies were actively guiding administrators to deploy critical...
By: Martin Sohn Christensen
Mar 24, 2026 • 55 min read
Read Post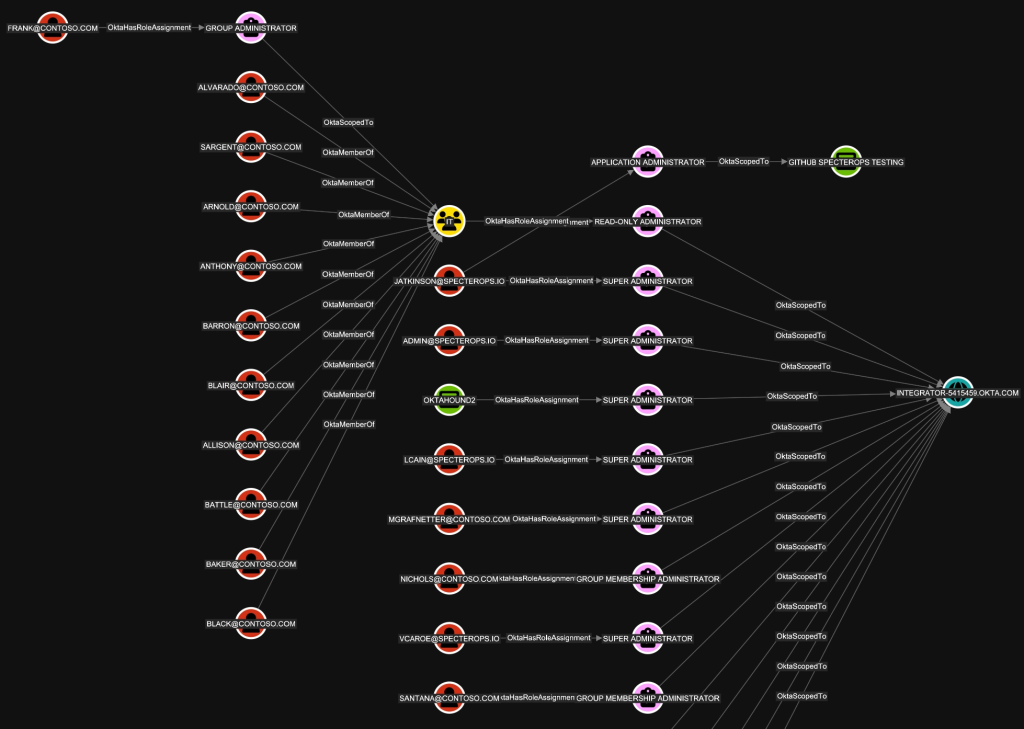
Research & Tradecraft
Discovering Unexpected Okta Attack Paths with BloodHound
TL;DR: OktaHound is a new data collector for the Okta Platform that ingests information about entities...
By: Michael Grafnetter
Mar 23, 2026 • 15 min read
Read Post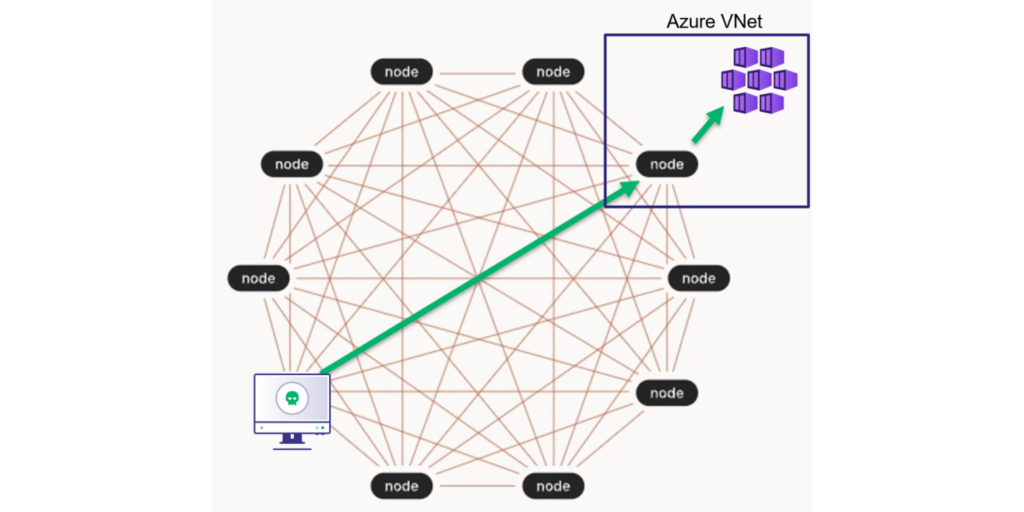
Research & Tradecraft
TL;DR: This post introduces red team operators to Tailscale concepts and tradecraft that can be leveraged...
By: Andrew Luke
Mar 12, 2026 • 15 min read
Read Post
Research & Tradecraft
Emergent Architectural Leakage in Frontier Models: The Dual-Claude Phenomenon
TL;DR: A pleasant evening conversation last summer with Claude resulted in a possible disclosure of its...
By: Max Andreacchi
Mar 11, 2026 • 12 min read
Read Post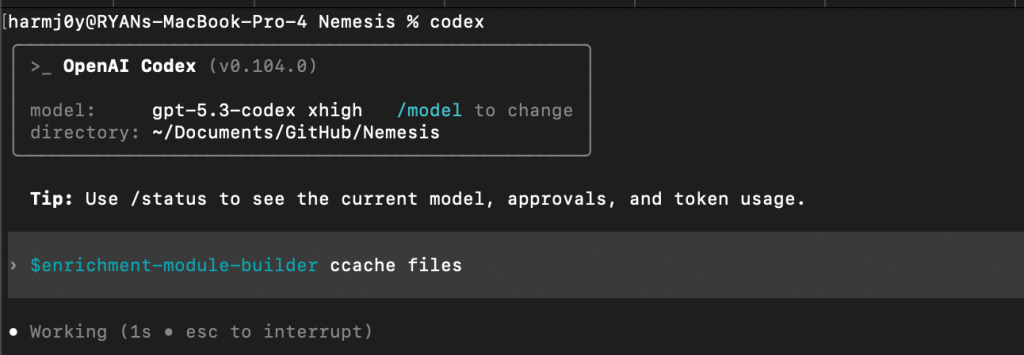
Research & Tradecraft
The Nemesis 2.X Development Guide
TL;DR: Nemesis 2.X makes it easy to extend the platform – this guide walks through creating...
By: Will Schroeder, Lee Chagolla-Christensen
Mar 10, 2026 • 16 min read
Read Post
Research & Tradecraft
TL;DR: Nemesis 2.2 automates the entire DPAPI decryption chain – from SYSTEM/user masterkeys through CNG keys...
By: Will Schroeder, Lee Chagolla-Christensen
Mar 4, 2026 • 16 min read
Read Post
Research & Tradecraft
TL;DR: Nemesis 2.2 introduces a number of powerful new features focusing on large container processing, data...