blog category
Research & Tradecraft
Research & Tradecraft
TL;DR: Nemesis 2.2 introduces a number of powerful new features focusing on large container processing, data...
By: Will Schroeder, Lee Chagolla-Christensen
Feb 25, 2026 • 22 min read
Read Post
Research & Tradecraft
Mapping Deception Solutions With BloodHound OpenGraph – Configuration Manager
TL;DR: At SpecterOps, we look at Attack Path Management from multiple perspectives, including those of identifying...
By: Joshua Prager
Feb 19, 2026 • 20 min read
Read Post
Research & Tradecraft
STOP THE CAP: Making Entra ID Conditional Access Make Sense Offline
TL;DR: Conditional Access is powerful but hard to reason about once policies start to overlap. CAPSlock...
By: Lee Robinson
Feb 17, 2026 • 18 min read
Read Post
Research & Tradecraft
V8 Heap Archaeology: Finding Exploitation Artifacts in Chrome’s Memory
TL;DR : This post aims to introduce readers to the anatomy and detection of JavaScript memory corruption...
By: Liam D.
Feb 11, 2026 • 17 min read
Read Post
Research & Tradecraft
Weaponizing Whitelists: An Azure Blob Storage Mythic C2 Profile
TL;DR: Mature enterprises lock down egress but often carve out broad exceptions for trusted cloud services....
By: Andrew Gomez, Allen DeMoura
Jan 30, 2026 • 10 min read
Read Post
Research & Tradecraft
Hacking Humans: Social Engineering and the Psychology
TL;DR : Social engineering engagements are the most exciting and heart pumping, “in my opinion”. It...
By: John Wotton
Jan 23, 2026 • 12 min read
Read Post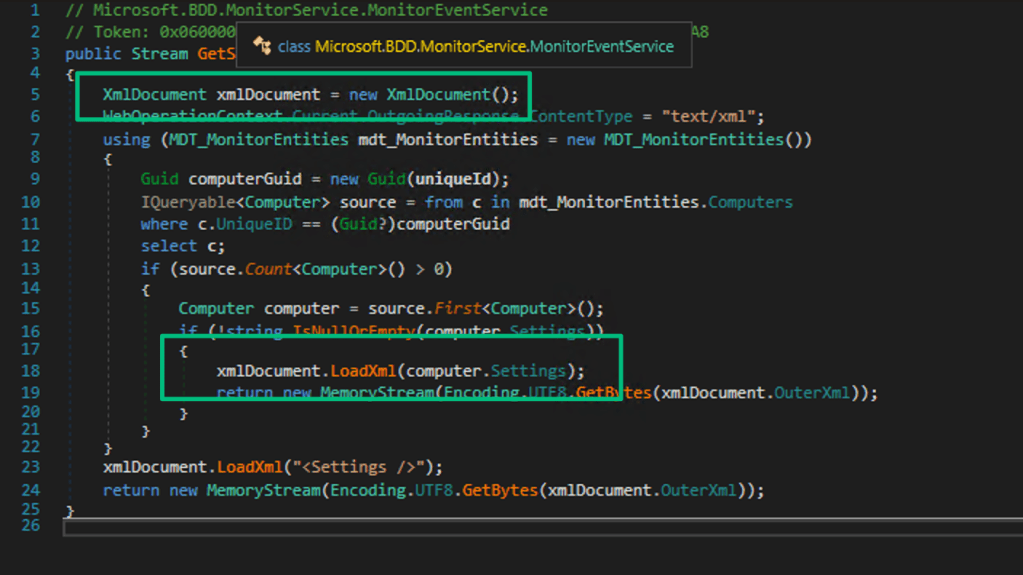
Research & Tradecraft
Task Failed Successfully – Microsoft’s “Immediate” Retirement of MDT
TL;DR – After reporting vulnerabilities found in MDT, Microsoft chose to retire the service rather than...
By: Garrett Foster
Jan 21, 2026 • 12 min read
Read Post
Research & Tradecraft
Updates to the MSSQLHound OpenGraph Collector for BloodHound
tl;dr: MSSQLHound, a PowerShell script that collects security information from remote MSSQL Server instances, now scans...
By: Chris Thompson
Jan 20, 2026 • 7 min read
Read Post
Research & Tradecraft
TL;DR – Windows Subsystem for Linux (WSL) is a powerful way for attackers to hide from...