BloodHound Enterprise Expands Beyond Microsoft: Mapping Identity Attack Paths Across Okta, GitHub, and Mac environments
For years, BloodHound has helped security teams answer a critical question: How could an attacker move through my environment?
Organizations around the world use BloodHound to map attack paths through Active Directory and Entra ID, revealing how privileges, permissions, and misconfigurations combine to put organizations at risk. These identity attack paths are the most reliable and favorite ways attackers move through enterprise environments.
But modern enterprises don’t operate within a single identity ecosystem.
Our identity infrastructure extends well beyond Microsoft platforms into identity providers, developer infrastructure, and device management platforms. Attackers understand this reality well. They regularly chain together privileges across multiple platforms to escalate access, control identities, and reach sensitive systems.
Today, we’re announcing a new BloodHound Enterprise platform with the first three official OpenGraph extensions that expand automated attack path analysis beyond the Microsoft ecosystem.
With support for Okta, GitHub, and macOS environments managed through Jamf, the new BloodHound Enterprise platform can now map identity relationships across platforms to help organizations uncover the attack paths attackers rely on and, more importantly, understand where to remediate them.
For BloodHound Enterprise customers interested in signing up for our early access program, click here.
Hybrid attack paths threaten the entire system.
Securing a single platform is really hard, just ask any Active Directory or Entra ID admin. We’ve used the analogy before but think of a single Active Directory domain or Entra ID tenant as a map of the United States. Instead of cities connected by roads, these environments are identities and resources linked by privileges and user behaviors. The number of attack paths within a single domain or tenant is higher than the number routes across within the United States. If that wasn’t bad enough, attack paths rarely stay confined to a single system.
An attacker who compromises a user account in Active Directory might leverage that access to escalate privileges in an identity provider. From there, they may gain access to device management platforms or developer infrastructure, eventually reaching sensitive systems like production environments or critical source code repositories.
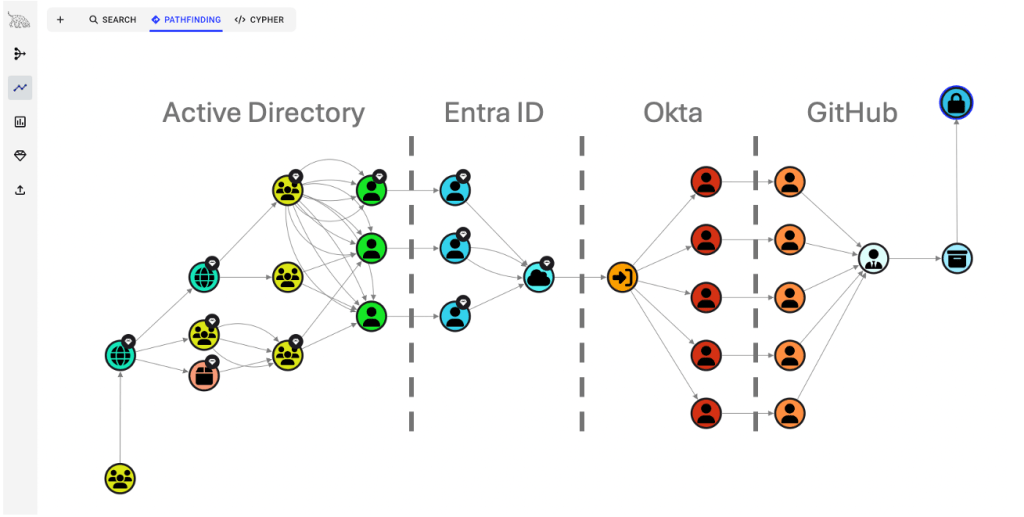
These chains of privilege are often difficult to detect because the relationships that enable them exist across multiple platforms. Worse yet, these configurations often sit between administrative teams. A Github admin and an Okta admin can configure everything “correctly” within the view of their given platform. However, the hybrid connections that connect these two platforms unravel the security of both.
The new BloodHound Enterprise is designed to expose exactly these kinds of relationships.
By mapping how identities and resources interact across environments, BloodHound helps defenders visualize the paths an attacker could take; and prioritize the remediation steps that break those paths before they can be exploited.
New BloodHound Enterprise and OpenGraph Extensions
Today we’re introducing a new BloodHound Enterprise platform with OpenGraph extensions, expanding attack path visibility into several critical platforms commonly found in modern enterprise environments.
Register for the new BloodHound Enterprise OpenGraph webinar on March 31.
Okta
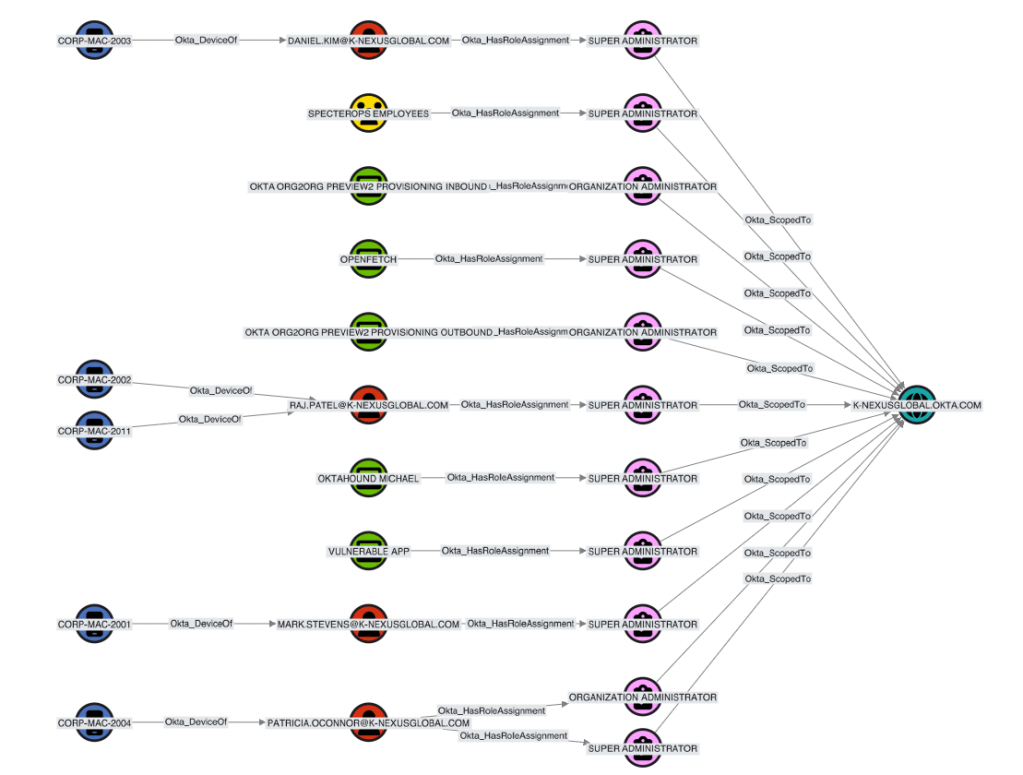
Okta plays a central role in many organizations as an identity provider, controlling access to applications and services across the enterprise.
BloodHound Enterprise now maps key identity relationships within Okta, helping defenders understand how administrative roles, application access, and identity configurations could enable privilege escalation or lateral movement.
This visibility helps security teams identify attack paths that originate, or terminate, within their identity provider infrastructure.
GitHub
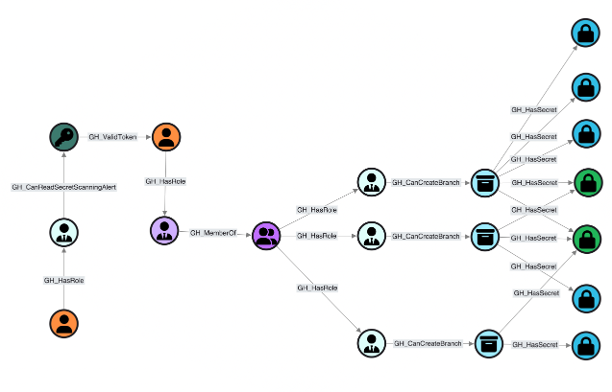
Developer platforms have become some of the most sensitive assets within modern organizations. Control over a critical repository can lead directly to infrastructure compromise, supply chain attacks, or exposure of sensitive intellectual property. In early testing, we helped a client uncover a critical attack path that allowed any employee provisioned through Okta to not only take over critical code repositories in Github, but also take over highly privileged AWS roles used for CI/CD.
BloodHound Enterprise now provides visibility into relationships within GitHub organizations and repositories, helping teams understand how privileges could be abused to gain control over critical codebases.
This allows defenders to identify attack paths that lead to the systems powering their applications and infrastructure.
Mac Environments
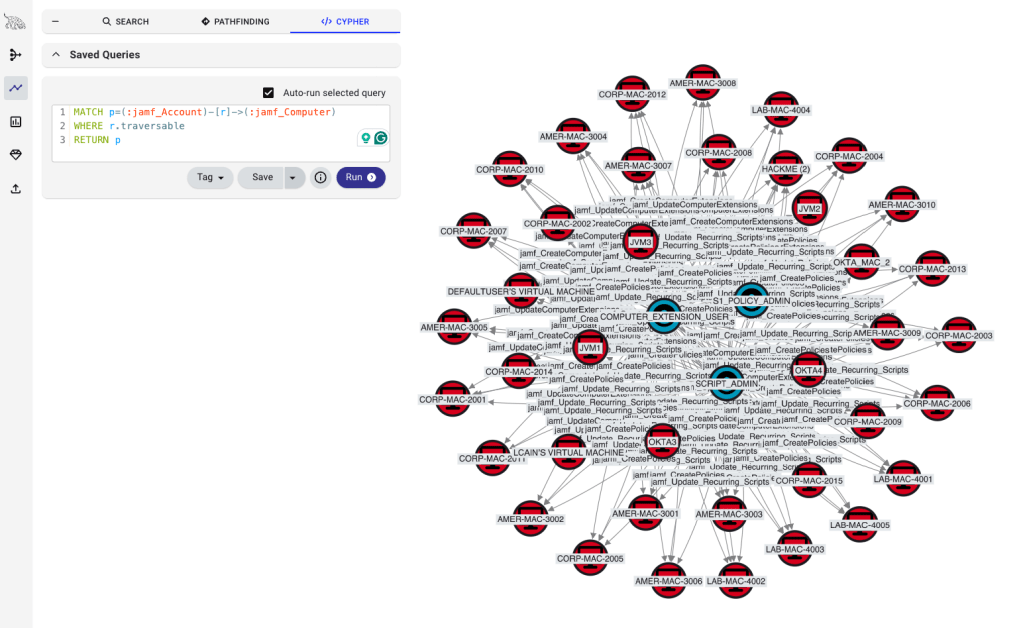
macOS adoption has grown rapidly across enterprises, and many organizations rely on Jamf to manage their Apple device fleets.
With BloodHound Enterprise support for Jamf environments, organizations can map relationships that influence control over their macOS fleet; such as administrative roles within Jamf or identities capable of managing devices. Our skilled adversary simulation teams have used Jamf to execute complete organization takeover without a single detection event firing.
This new coverage helps security teams understand how identity privileges could translate into device management control or fleet-level compromise.
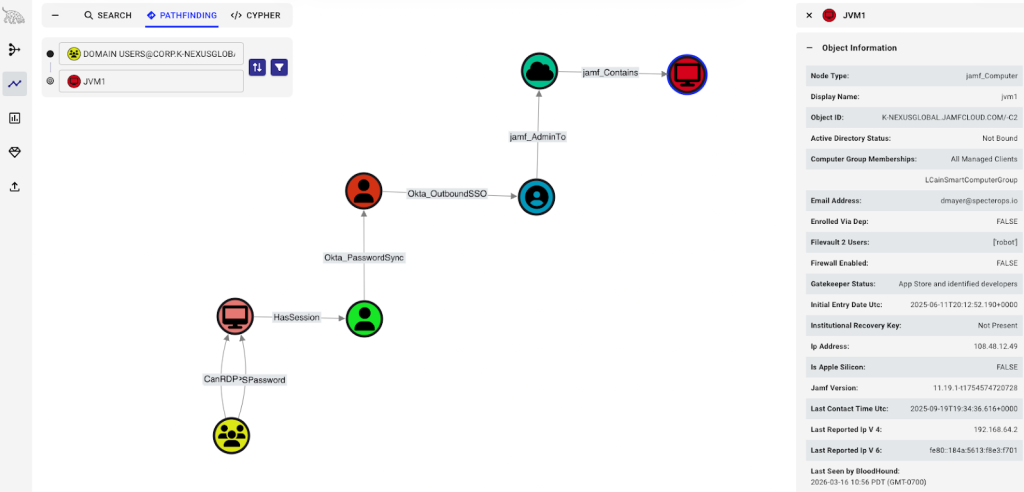
Furthermore, we’ve run into organization who use a combination of Okta and Jamf and don’t use AD/Entra ID at all. This new support combines to provide cross-platform visibility and misconfigurations to reduce risk.
We released our deep-dive on GitHub alongside this blog post and we’ll be diving deeper into the remaining platforms in dedicated blog posts in the coming weeks.
Privilege Zones is Now Generally Available
Alongside these new platform extensions, we’re also announcing the general availability of Privilege Zones and its inclusion in the new BloodHound Enterprise platform.
Privilege Zones allow organizations to define and protect critical security boundaries within their environment. These zones represent the systems, resources, or environments that would have the greatest impact if compromised.
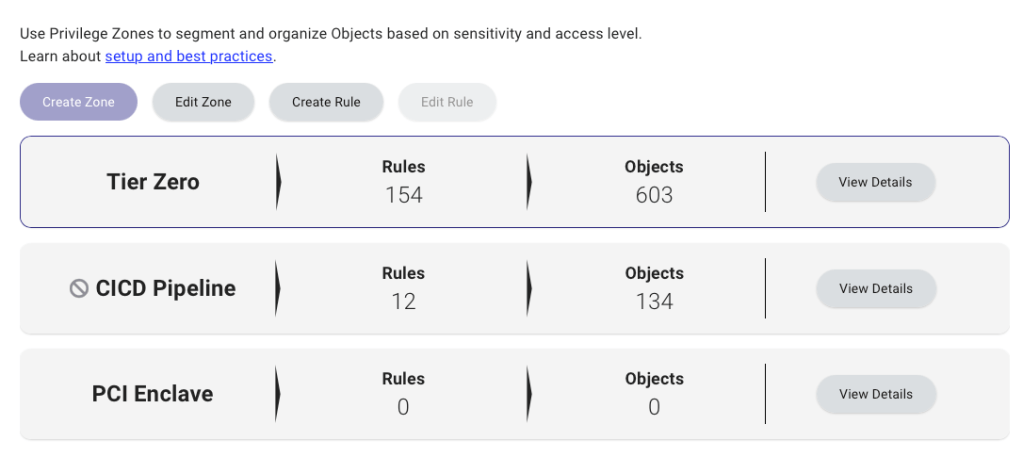
Examples include:
- Critical GitHub repositories
- macOS device management environments
- Okta Administrative control
- Control Plane / Privileged Access / Tier Zero Active Directory and Entra ID infrastructure
- Sensitive production environments
By defining Privilege Zones, BloodHound helps organizations focus on the attack paths that actually matter. Stop assuming by policy and start defining through technical controls. Security teams can quickly identify which privileges allow an attacker to cross those boundaries and take targeted remediation actions to prevent it.
Enhanced RBAC with Environment-Targeted Access Control
Large organizations often operate across multiple environments, subsidiaries, and operational teams. Managing security visibility across those environments requires careful access control.
With this release, BloodHound Enterprise now includes enhanced role-based access controls with environment-targeted access control.
This capability allows administrators to grant visibility to specific environments without exposing unrelated parts of the organization.
For example:
- A Jamf administrator can view risks related to their Jamf deployment but not Entra ID.
- An Active Directory domain admin in a subsidiary can see issues within their domain without visibility into the entire forest.
- Central security teams can maintain full organizational visibility while enabling delegated remediation across teams.
This ensures that the right people can see and act on the risks they own—without exposing sensitive information unnecessarily.
The New Family of BloodHound products
With these announcements, we’re introducing a new BloodHound Enterprise platform into the BloodHound suite of products. The new BloodHound Enterprise allows organizations to map attack paths across platforms and protect critical assets continuously with Privilege Zones.
BloodHound was created in 2016 to visualize the attack paths that threatened organizations. In 2021, BloodHound Enterprise was introduced to take back control and not just visualize but do so continuously, isolate choke points, and shut down risk at scale. We’re renaming this product to BloodHound Essentials as nearly every organization today utilizes a Microsoft backbone (AD or Entra ID) and, well….. let’s be honest, we kind of need BloodHound to understand effective privilege and how AD / Entra ID can be attacked.
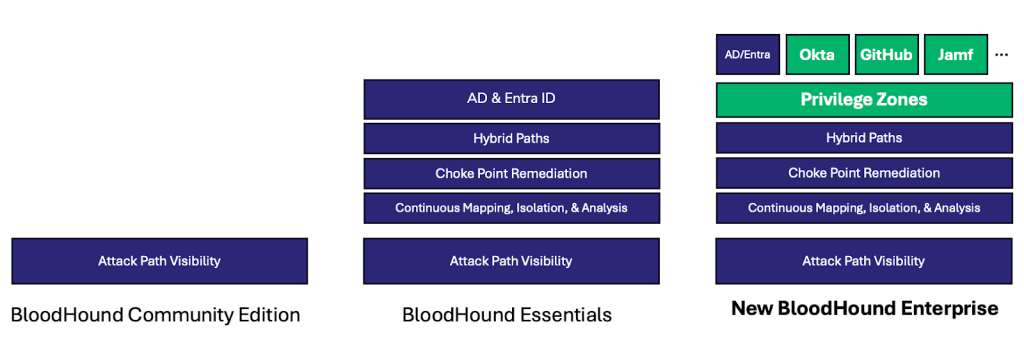
The new BloodHound Enterprise in 2026 recognizes that identities and attack paths aren’t isolated to Microsoft we see that in nearly every breach report, from SalesLoft to UNC6426s pivot from Github to AWS. We’re also expecting a ramp up in AI-executed attacks like this report from Sysdig where the actor was able to go from initial access to administrative privilege in 10 minutes. Detection is carrying too much load, it’s time to proactively prevent these attack paths and remove the adversary’s favorite target.
Looking Ahead to BloodHound Enterprise 9.0
Today’s announcement marks the beginning of a broader expansion of BloodHound Enterprise. The full BloodHound Enterprise 9.0 release, arriving April 13, will introduce additional capabilities that make it even easier to operationalize attack path management across platforms.
This includes:
- Enterprise collectors for Okta, GitHub, and Jamf with automated collection
- Automated choke point analysis that help pinpoint exactly where remediation will break critical attack paths
- Risk Posture Trend Analysis to establish a baseline and quantify improvements taken by remediations.
Together, these capabilities will help organizations continuously identify and eliminate identity attack paths across their environments.
Expanding the Future of Attack Path Defense
BloodHound began by transforming how organizations understand risk within Active Directory. Later, we expanded that visibility into Entra ID, helping defenders identify hybrid identity attack paths across cloud and on-prem environments.
With the introduction of Okta, GitHub, and Jamf support, BloodHound Enterprise is taking the next step, bringing attack path visibility to the broader identity ecosystem that modern organizations rely on every day.
This is only the beginning of where BloodHound will extend to in 2026. Because identity risk doesn’t stop at platform boundaries.
And neither should defenders.