blog category
BloodHound

BloodHound
Learn how modern attackers chain identity access across platforms—and how to uncover and break those paths...
By: Justin Kohler
Mar 18, 2026 • 8 min read
Read Post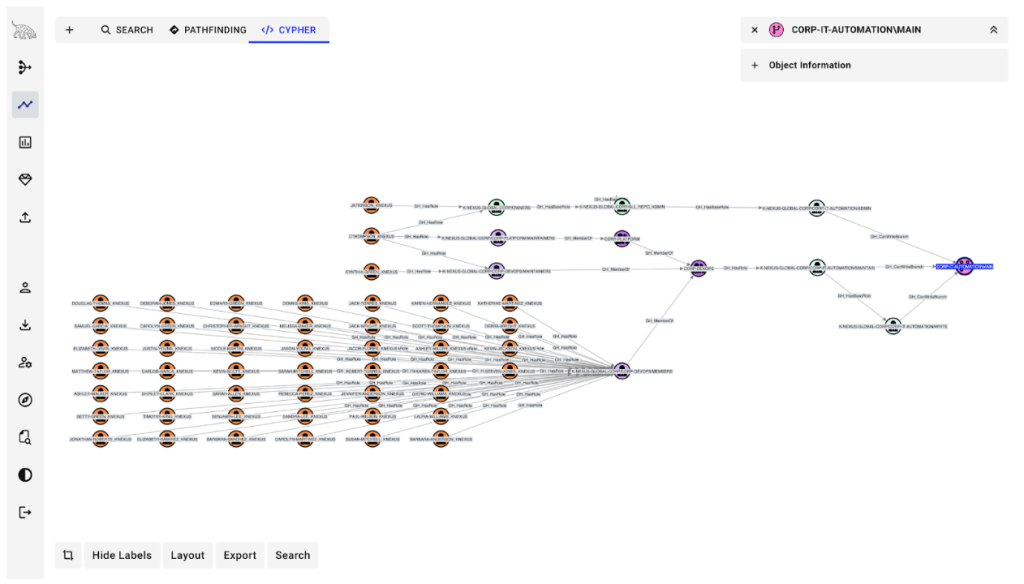
BloodHound
Introducing Attack Path Management for GitHub in BloodHound Enterprise
Learn how GitHub acts as both a target and pivot point in attack paths—and how to...
By: Jared Atkinson
Mar 18, 2026 • 10 min read
Read Post
BloodHound
Mapping Deception Solutions With BloodHound OpenGraph – Configuration Manager
TL;DR: At SpecterOps, we look at Attack Path Management from multiple perspectives, including those of identifying...
By: Joshua Prager
Feb 19, 2026 • 20 min read
Read Post
BloodHound
TL;DR : BloodHound Enterprise on-premises brings enterprise-grade identity attack path management to air-gapped, classified, and highly...
By: Sev Kocharian
Jan 29, 2026 • 5 min read
Read Post
BloodHound
Updates to the MSSQLHound OpenGraph Collector for BloodHound
tl;dr: MSSQLHound, a PowerShell script that collects security information from remote MSSQL Server instances, now scans...
By: Chris Thompson
Jan 20, 2026 • 7 min read
Read Post
BloodHound
MSSQL and SCCM Elevation of Privilege Vulnerabilities
TL;DR: I found two privilege escalation vulnerabilities, one in MSSQL (CVE-2025-49758) and one in Microsoft Configuration...
By: Chris Thompson
Jan 15, 2026 • 16 min read
Read Post
BloodHound
Introducing ConfigManBearPig, a BloodHound OpenGraph Collector for SCCM
tl;dr: Security researchers have discovered 30+ unique attack techniques targeting SCCM in the past several years,...
By: Chris Thompson
Jan 13, 2026 • 45 min read
Read Post
BloodHound
Mapping Deception with BloodHound OpenGraph
TL;DR As defensive postures continue to mature, deception technologies provide organizations the opportunity to harden defenses...
By: Ben Schroeder
Dec 23, 2025 • 27 min read
Read Post
BloodHound
Azure Seamless SSO: When Cookie Theft Doesn’t Cut It
TL;DR The cookie crumbled when it expired, but the attack path didn’t. Learn how BloodHound graph...