blog category
Research & Tradecraft
Research & Tradecraft
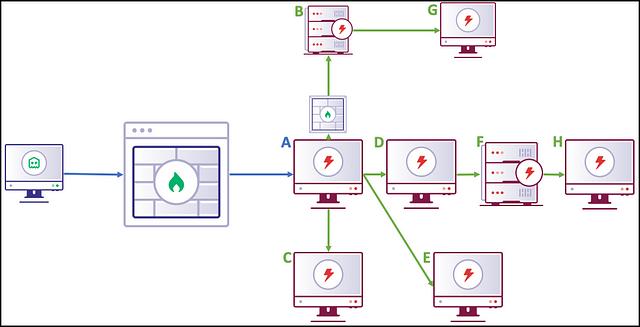
Designing Peer-To-Peer Command and Control
By: Ryan Cobb
May 1, 2019 • 19 min read
Read Post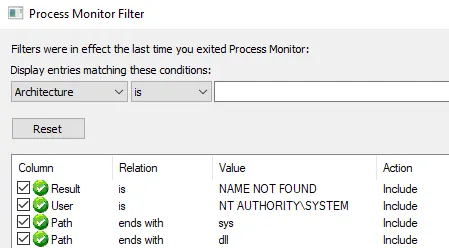
Research & Tradecraft
Lateral Movement — SCM and DLL Hijacking Primer
Summary As Defenders increase in maturity, the more they are able to leverage built-in utilities against...
By: Dwight Hohnstein
Apr 18, 2019 • 11 min read
Read Post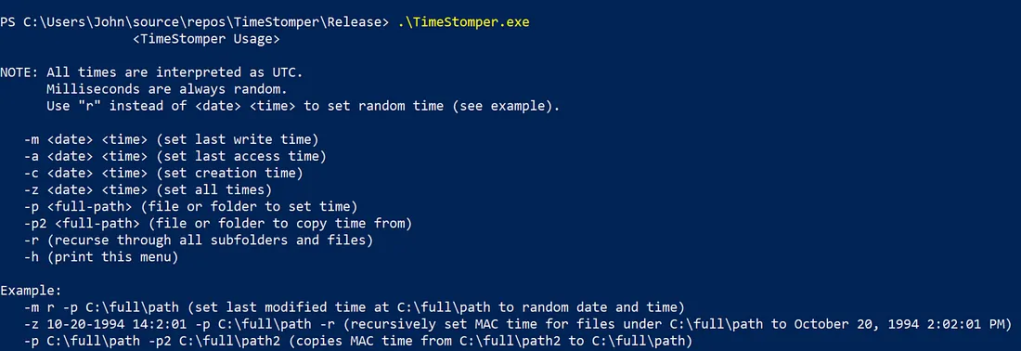
Research & Tradecraft
In this post, I will cover how to manipulate file times on the Windows OS. Manipulating...
By: Justin Bui
Apr 16, 2019 • 8 min read
Read Post
Research & Tradecraft
Merlin v0.7.0 Release & Roll-up
By: Russel Van Tuyl
Apr 12, 2019 • 10 min read
Read Post
Research & Tradecraft
Folder Actions for Persistence on macOS
By: Cody Thomas
Apr 8, 2019 • 9 min read
Read Post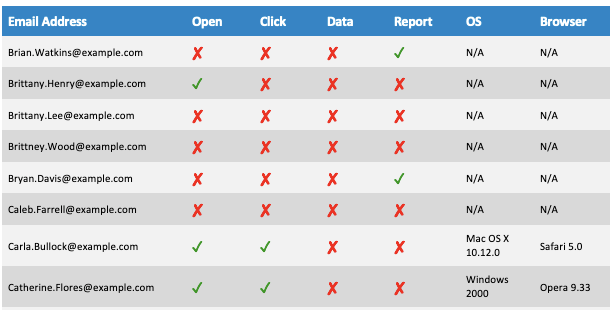
Research & Tradecraft
The Hitchhiker’s Guide To Initial Access
Abusing Bias — Part 2 (Mostly) Harmless If aliens started monitoring Earth, it would appear that...
By: Kelly Villanueva
Mar 8, 2019 • 12 min read
Read Post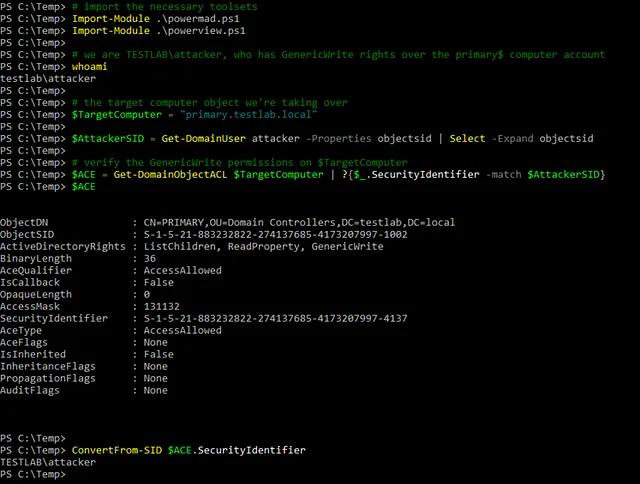
Research & Tradecraft
A Case Study in Wagging the Dog: Computer Takeover