Tag
Proxy
Proxy
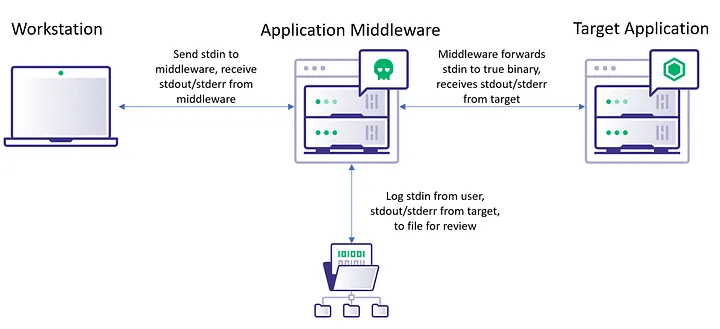
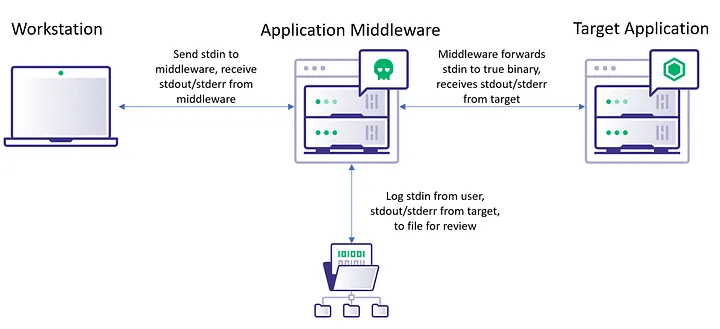
Summary By using path hijacking and modification on Unix-like machines, we can achieve pseudo-keylogging functionality by...
Proxy
Summary By using path hijacking and modification on Unix-like machines, we can achieve pseudo-keylogging functionality by...