Don’t Just Detect Attacks—Prevent Them Entirely
Eliminate attack paths to your critical assets
Attackers evade detection by assuming human and non-human identities, accessing valid credentials and sessions, and blending in with expected behavior as they reach their objectives. BloodHound Enterprise eliminates the paths that enable cross-environment attacks on your critical applications and assets.

See how BloodHound Enterprise uncovers and eliminates hidden threats to your vital systems
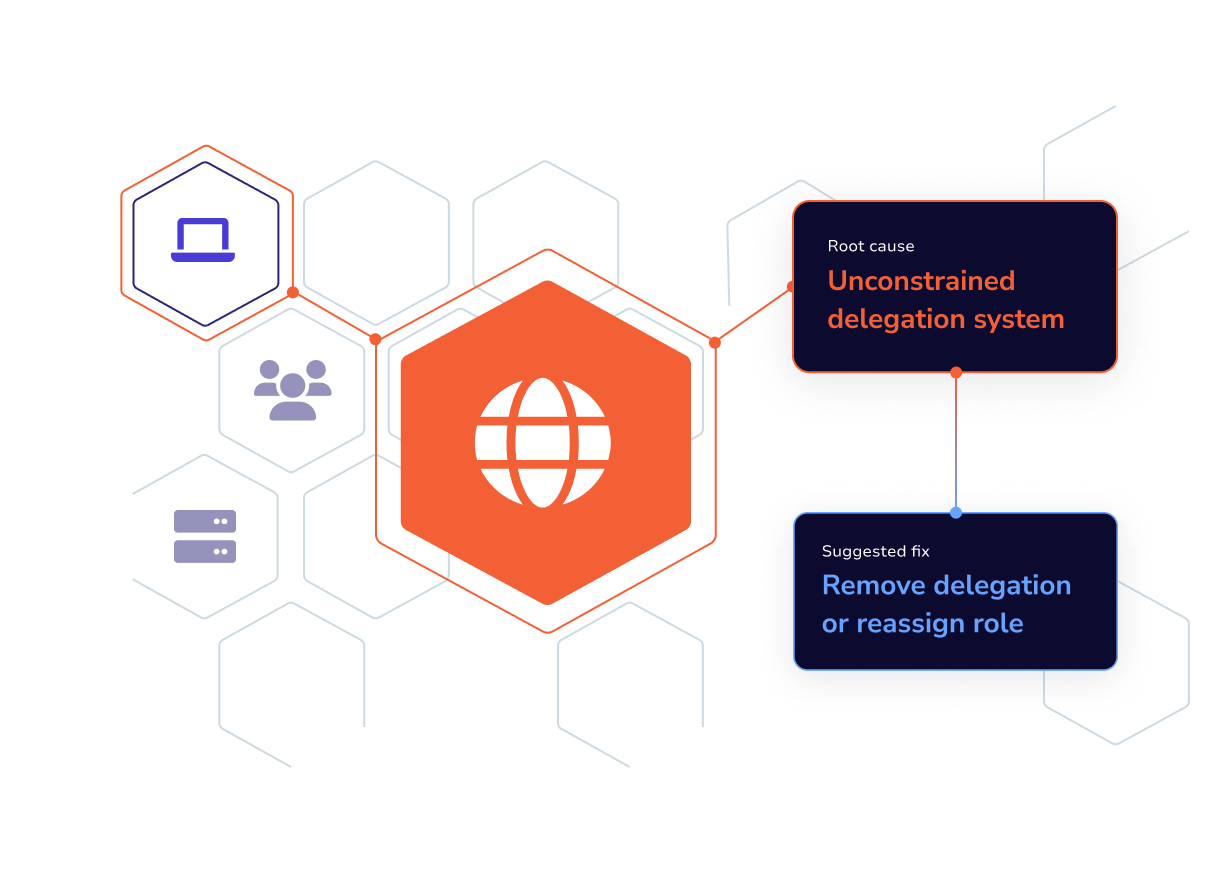
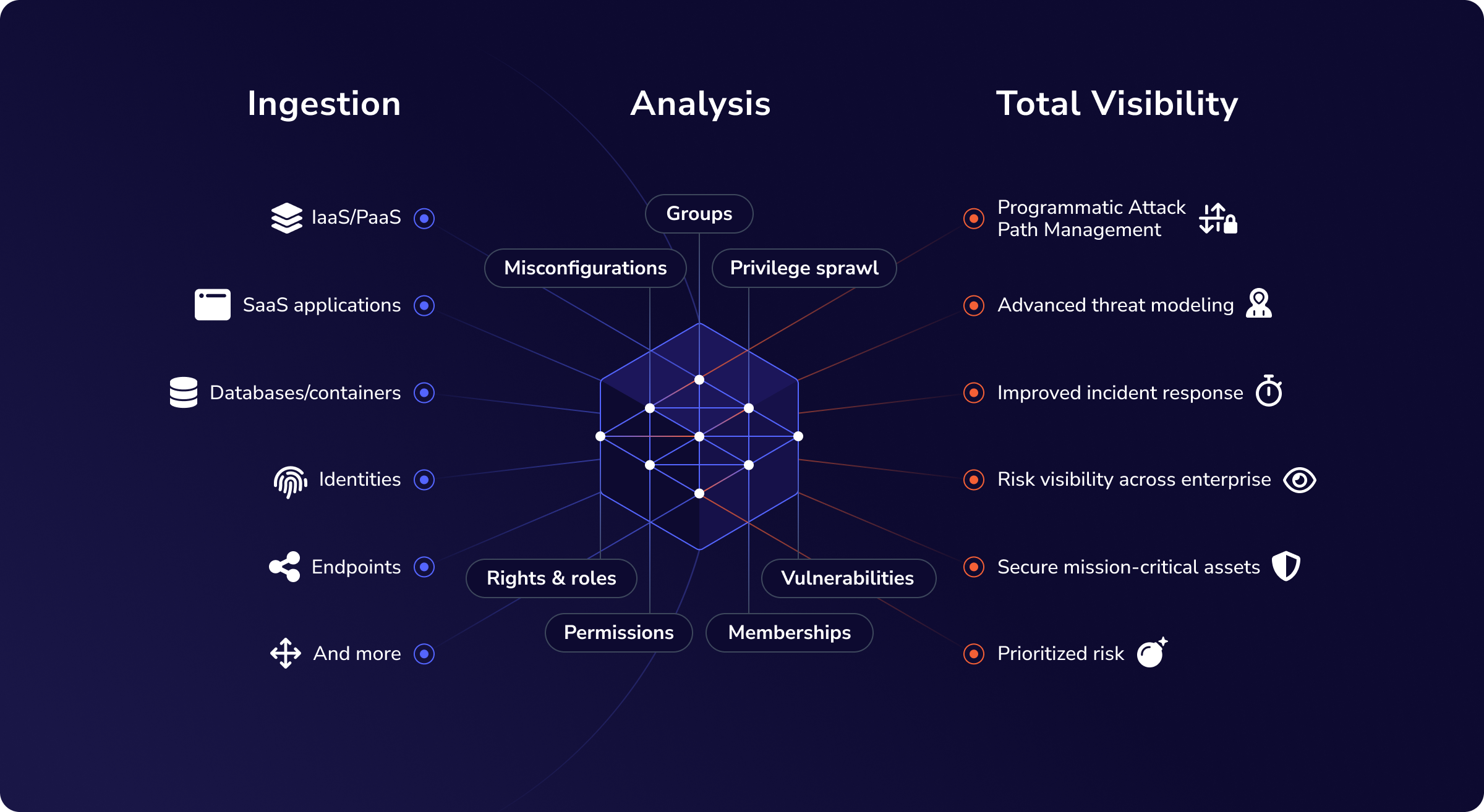
The most advanced identity attack path map available
Bring clarity to identity sprawl while protecting what matters most. Map, prioritize, and remediate identity attack paths and the conditions that create them.
See how attackers can pivot across systems to reach high value targets
Create a continuous Attack Path Management (APM) practice
Backed by decades of SpecterOps research, training, and offensive security expertise
Create Privilege Zones around your critical assets
Define multiple privilege tiers for business-critical applications, regulated systems, and sensitive groups or data within your environment to extend attack path management beyond traditional identity infrastructure.
Extend Least-Privilege Enforcement with Privilege Zone Analysis:
Build isolated Privilege Zones to protect critical assets
Visualize and resolve privilege zone violations putting you at risk
Understand gaps in least privilege coverage and how to correct them
Prevent cross-environment breaches
BloodHound Enterprise OpenGraph extensions for Okta, GitHub, and Mac extend identity attack path management across the enterprise.
Turn BloodHound OpenGraph loose on the attack paths leading to your critical assets to understand how attackers pivot between identity platforms to reach them. Then remediate the risk with expert guidance as part of a continuous APM practice.
- Eliminate escalation paths in Okta and Jamf that enable access to critical assets
- Prevent cross-environment attacks
- Understand risk in multi-identity environments
- Protect GitHub repositories from malicious tampering or deletion
Improve the effectiveness of your security stack
Integrate your identity and security operations workflows with BloodHound Enterprise to add attack path data as part of a holistic security practice.
Enhance Incident Response with key attack path details
Provide key attack path insight to bolster SIEM logs and alerts
Assign ownership and SLAs to attack paths to track remediation efforts
Quickly know which alerts matter most by adding attack path context
Identity is the adversary’s favorite target
As identities evolve and environments expand, static defenses fall short.
BloodHound Enterprise helps you stay ahead by operationalizing Identity APM.
Establish a continuous, measurable Identity Attack Path Management practice
Strengthen your existing stack with BloodHound Enterprise’s integrated analysis and workflows
Eliminate the attack paths behind many of your alerts—and reduce detection noise at the source
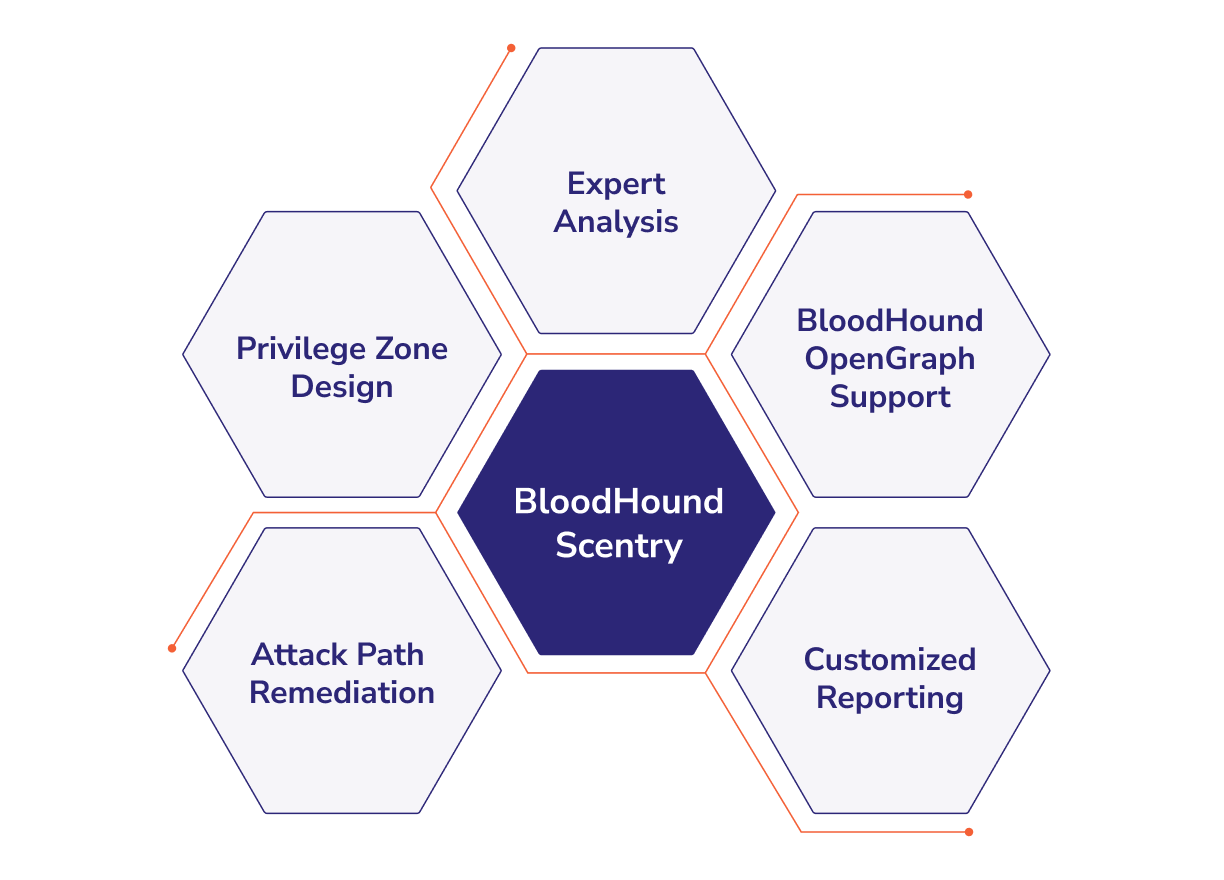
Accelerate your APM practice with help from BloodHound Scentry
BloodHound Scentry combines the power of BloodHound Enterprise with the expertise of SpecterOps to accelerate APM practices.
Scentry provides:
Tailored guidance for attack path remediation
Advanced analysis for emerging threats
OpenGraph support to expand coverage
Privilege Zone design to protect critical assets
100
M+
Attack paths remediated
Hundreds of millions of attack paths remediated with BloodHound Enterprise.
35
%
Risk reduction
BloodHound Enterprise customers see an average 35% reduction of risk in the first 30 days.
17
K+
Paths cut per choke point
On average, cutting a single choke point severs access to more than 17,000 attack paths.
What Practitioners Are Saying
Validated by hands-on operators and strategic teams alike. These real-world testimonials show how organizations use BloodHound Enterprise to reduce identity risk at scale.
Learn More About
Attack Path Management
See how BloodHound Enterprise eliminates millions of attack paths while focusing your defenses on the routes attackers actually use to reach your critical assets.