OpenGraph for BloodHound Enterprise
Extend Identity Attack Path Management Across Hybrid Environments
OpenGraph for BloodHound Enterprise extends Attack Path Management beyond Active Directory, enabling security teams to identify and eliminate hybrid identity attack paths across platforms such as Okta, GitHub, and Jamf.
Reveal and eliminate the pathways attackers use to reach critical assets.

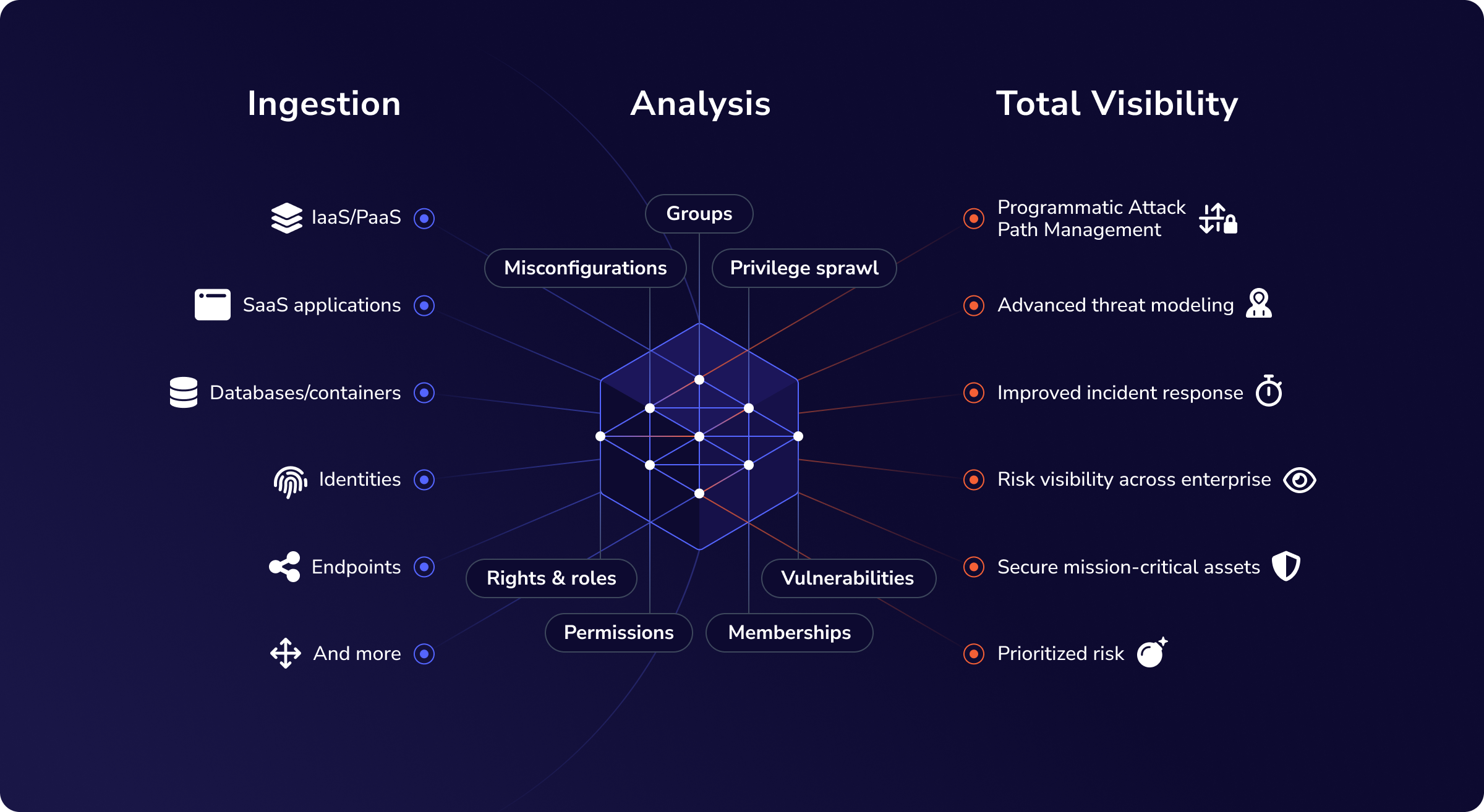
Graphing modern identity risk
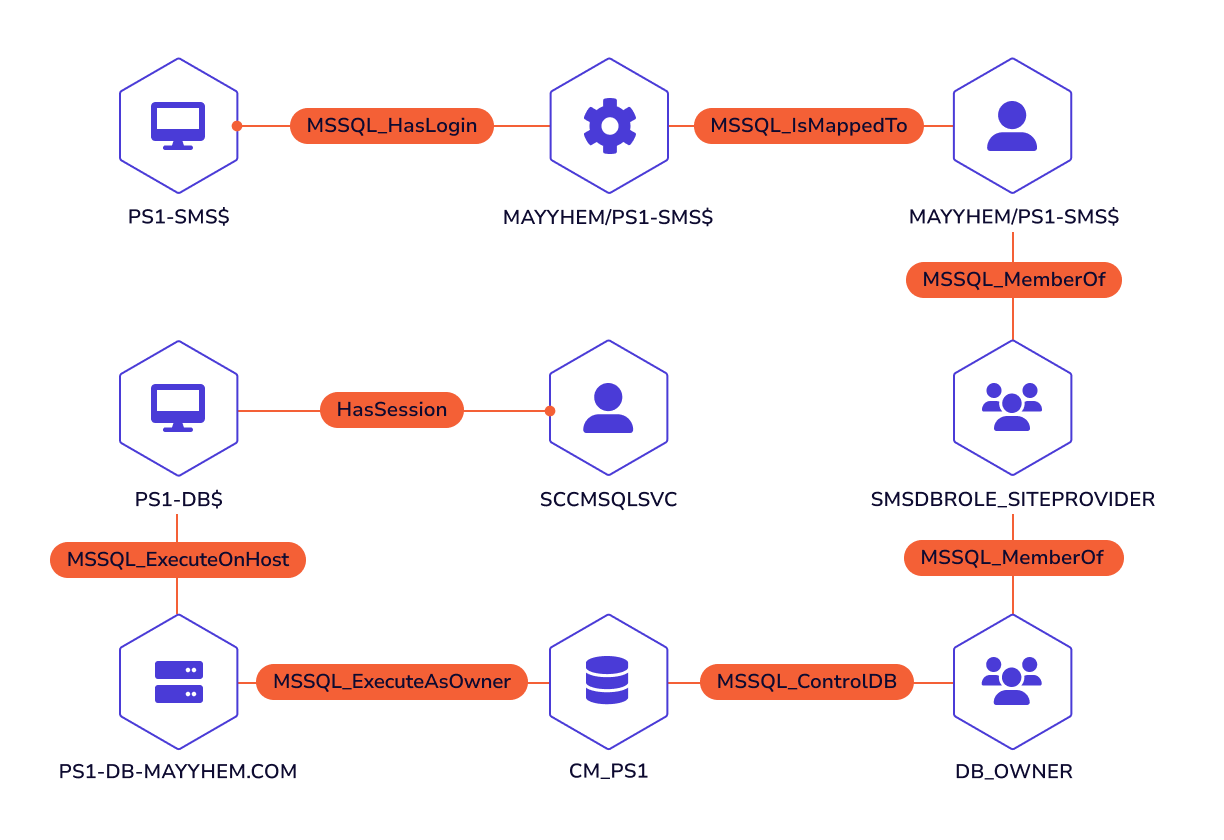
Graphs built for cloud infrastructure or endpoint security cannot expose the identity relationships attackers exploit to reach critical assets. Modern attacks span identity providers and cloud and developer environments. OpenGraph unifies identity data across these platforms into a single attack path graph. Security teams can identify and prioritize hybrid attack paths and access remediation guidance before they are exploited.
The graph of modern identity infrastructure
OpenGraph expands BloodHound Enterprise to help organizations identify and remediate identity attack paths across platforms.
Built in collaboration with the global BloodHound open source community, OpenGraph extends Attack Path Management beyond traditional identity infrastructure and across developer systems, identity providers, and Mac environments.
Explore OpenGraph for Okta, GitHub, and Jamf (Mac) environments
Discover attack paths everywhere
Instead of investigating isolated alerts, OpenGraph helps security teams focus on the identity exposures that place critical assets at risk.
Identify hybrid identity attack paths across Okta, GitHub, Jamf, and Active Directory
Discover identity misconfigurations across SaaS platforms and identity providers
Visualize how attackers move through identity relationships
Prioritize remediation based on real attack paths
Reduce hybrid identity risk
With OpenGraph, identity and security teams can identify and remediate attack paths across identity providers, applications, and repositories.
Detect identity misconfigurations and escalation risks across Okta, GitHub repositories, and Jamf-managed Mac devices
Define privilege tiers and identify violations across business-critical systems and regulated environments.
Restrict identity access across domains and environments to reduce identity-driven exposure.
Operationalize identity attack path management
Move from reactive identity security to proactive attack path reduction with continuous visibility and remediation.
Continuously identify hybrid identity attack paths
Prioritize exposures that threaten critical assets
Safely remediate identity misconfigurations
Build mature Identity Attack Path Management practices
See BloodHound OpenGraph in Action
Discover hybrid identity attack paths across Okta, GitHub, and Jamf environments and learn how BloodHound Enterprise reveals and prioritizes identity risk across your environment.
Request a BloodHound Enterprise Demo