The BloodHound Enterprise Difference
Attackers evade detection by assuming human and non- human identities, accessing valid credentials and sessions on those identities, and blending in with expected behavior as they reach their objectives. BloodHound Enterprise eliminates the attack paths that enable cross- environment attacks on your critical applications and assets.

See how BloodHound Enterprise uncovers and eliminates hidden threats to your vital systems
BloodHound Enterprise Protects the Critical Assets of Leading Global Enterprises
BloodHound Enterprise is used by customers to monitor and manage…
500k
Critical assets
110M
Identities
>5B
Relationships
650B
Attack Paths
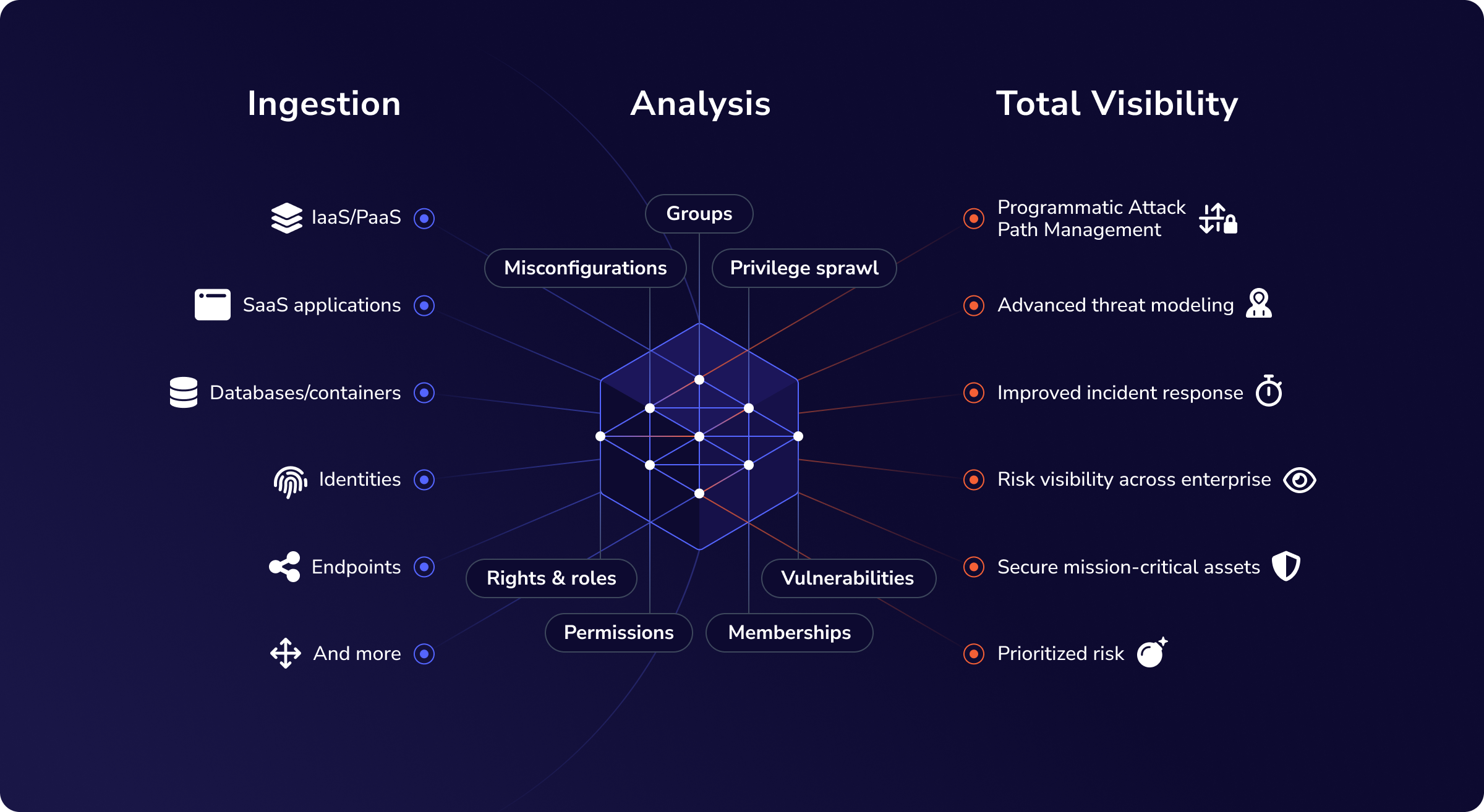
Extended Attack Path Management Coverage
Enterprise identity risk is a cross-platform problem. Users authenticate through cloud and on-premises identity. BloodHound Enterprise is built for the reality of cross platform attack paths.
- Continuous attack path management across Active Directory, Microsoft Entra ID, Okta, GitHub, and Jamf-managed macOS environments
- Create Privilege Zones to protect critical assets throughout your enterprise
- Adversarial perspective of cross-environment risk
- More Enterprise OpenGraph extensions available soon
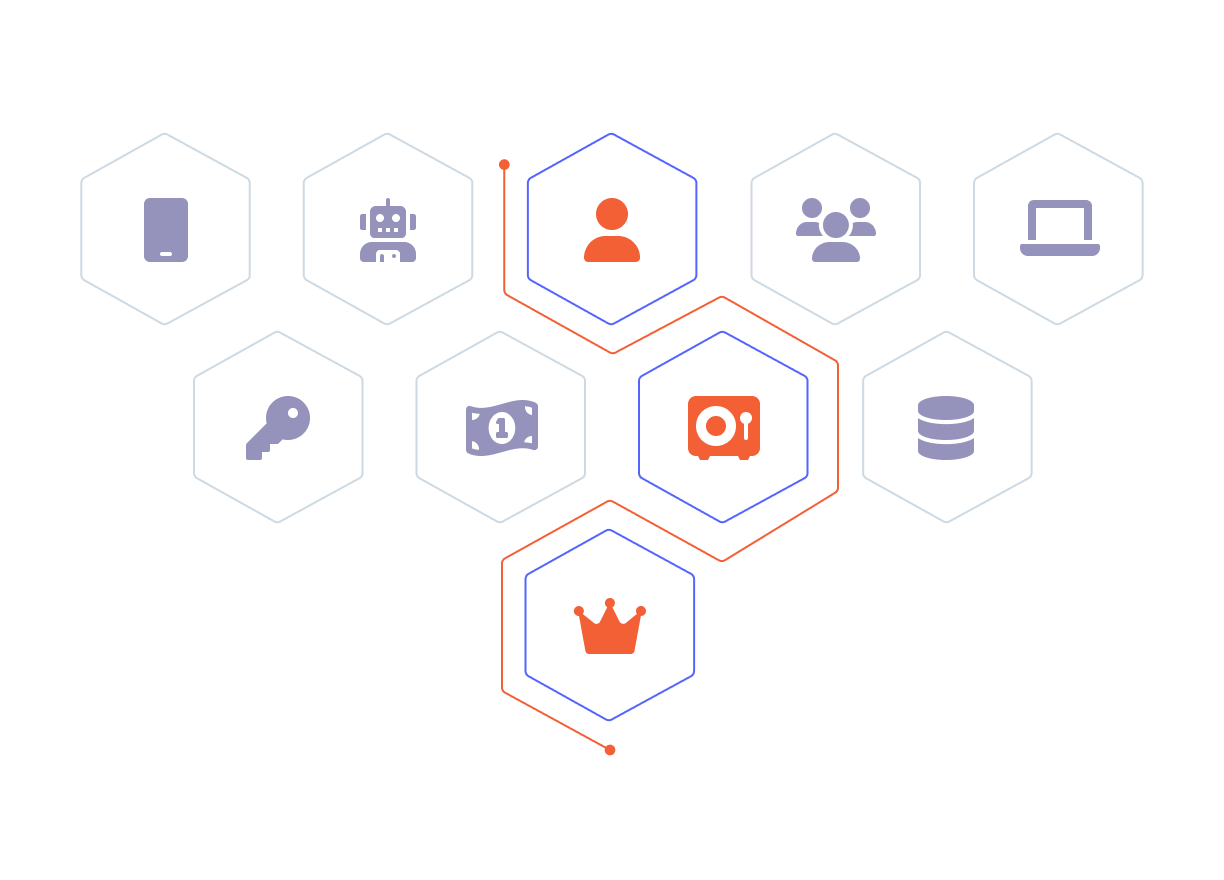
Privilege Zones built to protect critical assets
BloodHound Enterprise Privilege Zones allow organizations to define any asset, group, or environment as a protected zone with continuously monitored attack paths.
This extends protection beyond Tier Zero to every critical asset the business depends on:
Risky groups and resources — Resources, users, or groups that are not Tier Zero but their impact, if compromised, would be similarly impactful
Regulatory and compliance enclaves — HIPAA, PCI DSS, and other regulated environments requiring auditable access path governance
Code repositories and cloud data stores — High-value data stores and code repositories represent significant breach and exfiltration risk
OpenGraph environments — Okta tenants, GitHub organizations, and Jamf-managed device groups, each governed as a defined zone
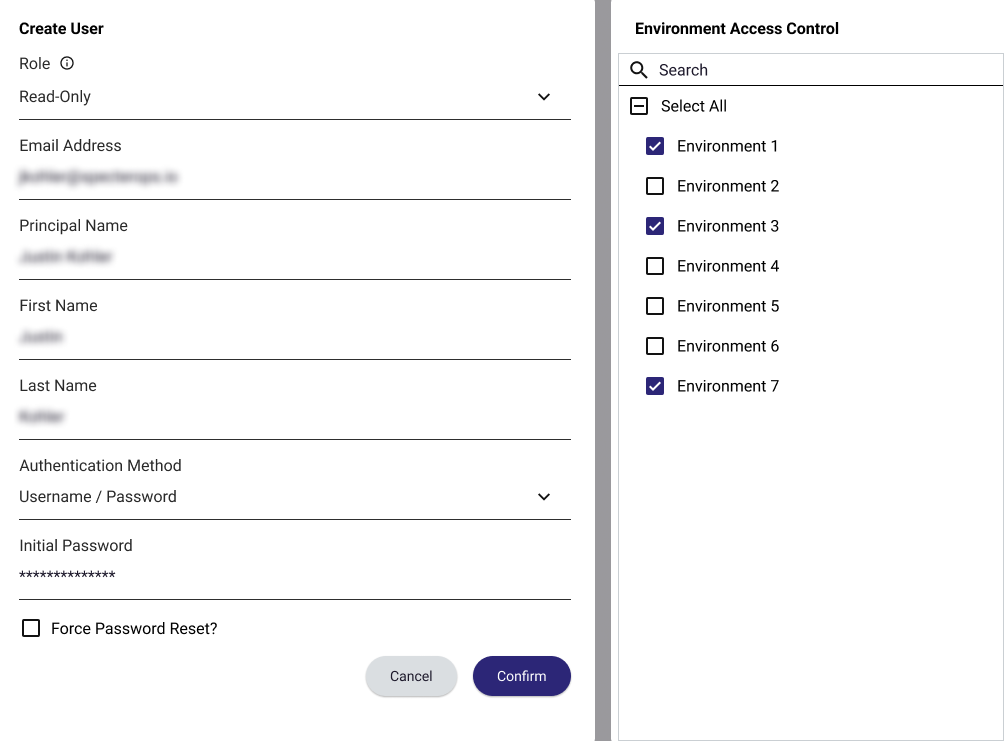
Enterprise-grade security controls
BloodHound Enterprise has enhanced security controls built for Attack Path Management in complex environments.
Environment-Targeted Access Controls (ETAC) enforce least privilege inside the platform itself, restricting each user’s visibility to only the domains, tenants, and environments they are authorized to see. Designed for organizations managing multiple lines of business, acquired entities, or strict separation of duties requirements.
Bring Your Own Key (BYOK) gives organizations full control over the encryption keys protecting BloodHound Enterprise data, satisfying data sovereignty requirements and supporting regulated industries without any trade-off in platform visibility or performance.
On-Premises Deployment and FedRAMP-High Authorization are available for organizations with data residency requirements.
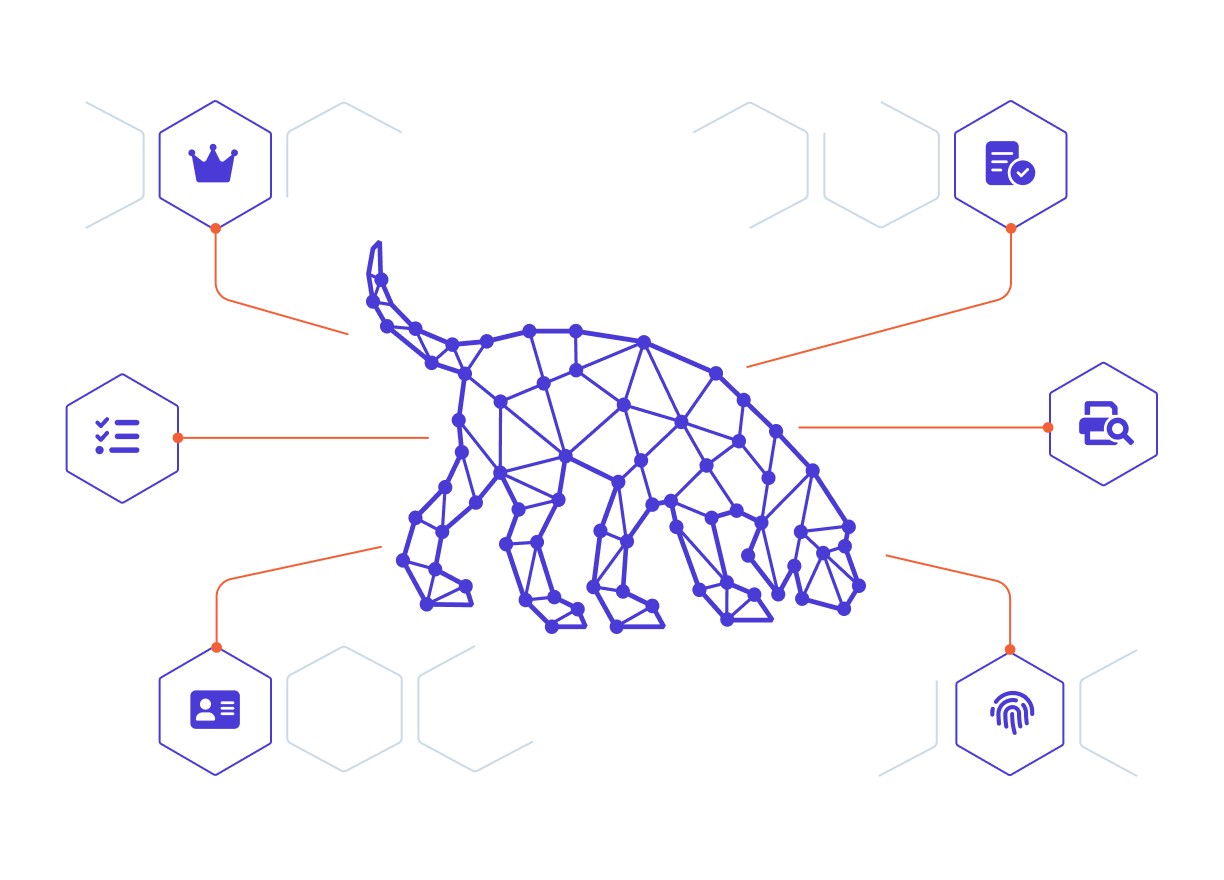
Dedicated technical account management
BloodHound Enterprise customers work with a named Technical Account Manager. Your TAM guides deployment, optimizes data collection across all environments, and runs regular monthly sessions to build internal capability and keep your program advancing. When complex issues arise, you have a direct line to someone who knows your environment.
BloodHound Enterprise vs. BloodHound Essentials
|
Capability |
Bloodhound Enterprise |
BloodHound Essentials |
|
Privilege Zones |
Unlimited |
|
|
Attack Path Protection: AD & Entra ID |
|
Included |
|
OpenGraph Extensions (Okta, GitHub, Jamf) |
3 included |
|
|
Environment-Targeted Access Controls (ETAC) |
|
|
|
Bring Your Own Key (BYOK) |
|
|
|
On-Premises Deployment |
Available |
|
|
FedRAMP-High |
Available |
|
|
BloodHound Scentry |
Available |
Available |
|
Technical Account Management |
Named TAM |
Pooled TAM |
Which BloodHound is right for you?
BloodHound Enterprise is the complete attack path management program for protecting critical assets across the hybrid enterprise.
For organizations limited to Active Directory and Entra ID today and focused on Tier0 only, BloodHound Essentials offers targeted value and identity risk reduction.
For everyone operating across a modern hybrid environment, BloodHound Enterprise is where the program belongs.