blog category
Research & Tradecraft
Research & Tradecraft
AWS ReadOnlyAccess: Not Even Once
By: Daniel Heinsen
Aug 27, 2021 • 9 min read
Read Post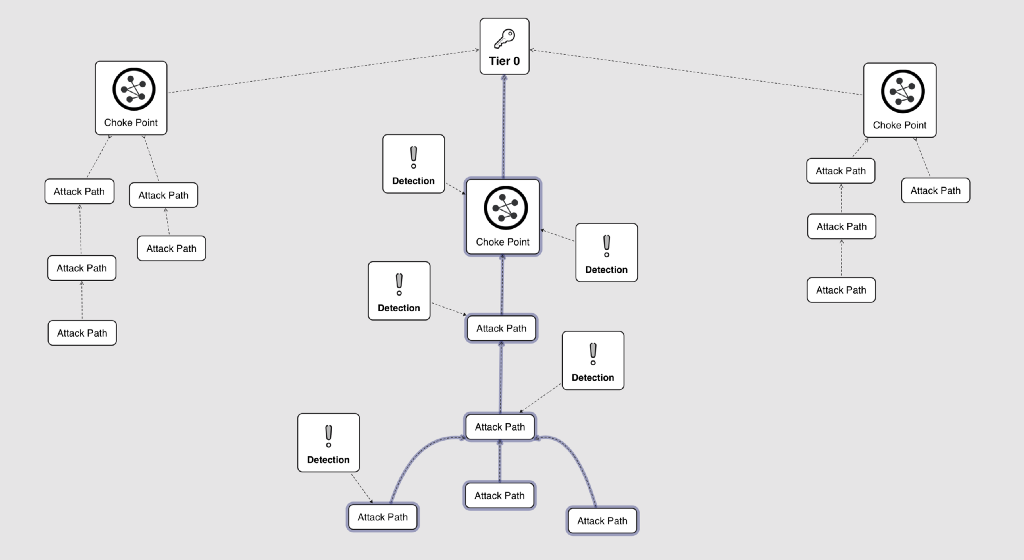
Research & Tradecraft
Entity Based Detection Engineering with BloodHound Enterprise
Critical Attack Path with Auditing Table of Contents Introduction Enterprise Access Model BloodHound and Detection BloodHound Enterprise Entity Based...
By: Joshua Prager
Aug 18, 2021 • 13 min read
Read Post
Research & Tradecraft
1Password Secret Retrieval — Methodology and Implementation
Background and Motivation 1Password is a password manager developed by AgileBits Inc., providing a place for users to store...
By: Dwight Hohnstein
Aug 17, 2021 • 17 min read
Read Post
Research & Tradecraft
Playing Detection with a Full Deck
By: Jared Atkinson
Aug 16, 2021 • 12 min read
Read Post

Research & Tradecraft
L;DR Active Directory Certificate Services has a lot of attack potential! Check out our whitepaper “Certified Pre-Owned:...
By: Will Schroeder
Jun 17, 2021 • 28 min read
Read Post
Research & Tradecraft
Shadow Credentials: Abusing Key Trust Account Mapping for Account Takeover
By: Elad Shamir
Jun 17, 2021 • 12 min read
Read Post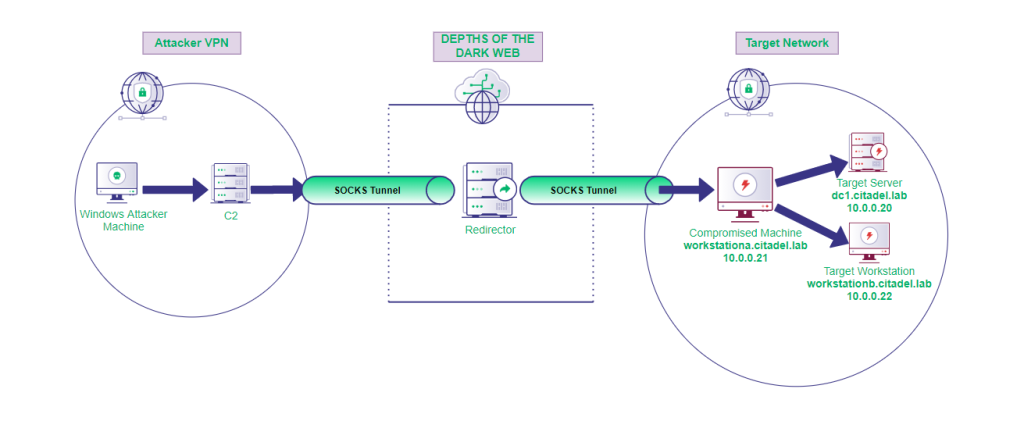
Research & Tradecraft
Proxy Windows Tooling via SOCKS
By: Nick Powers
Jun 10, 2021 • 14 min read
Read Post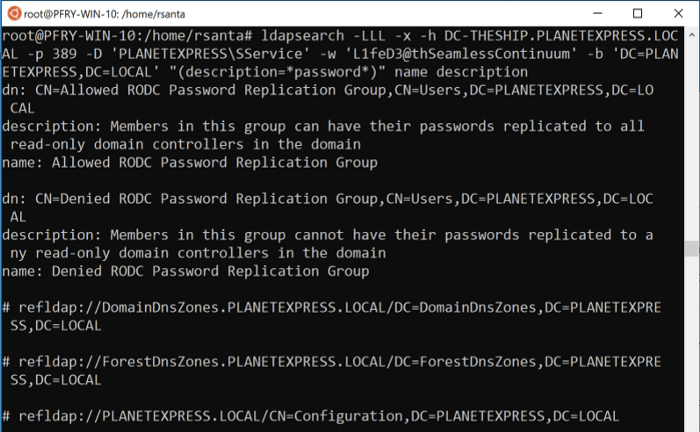
Research & Tradecraft
An Introduction to Manual Active Directory Querying with Dsquery and Ldapsearch
Introduction Let’s be honest, BloodHound and PowerView are objectively better tools for querying, enumerating, and investigating Active Directory (AD). They...