blog category
Research & Tradecraft
Research & Tradecraft
Learning Machine Learning Part 1: Introduction and Revoke-Obfuscation
For the past two years I’ve been trying to get a grasp on the field of...
By: Will Schroeder
Apr 5, 2022 • 34 min read
Read Post
Research & Tradecraft
Revisiting Phishing Simulations
This post was written by Matt Hand and the rest of the SpecterOps team. Overview SpecterOps...
By: Matt Hand
Mar 9, 2022 • 20 min read
Read PostResearch & Tradecraft
Introducing BloodHound 4.1 — The Three Headed Hound
Introducing BloodHound 4.1 — The Three Headed Hound Prior Work Analyzing Active Directory attack paths using graph theory is...
By: Andy Robbins
Feb 9, 2022 • 5 min read
Read Post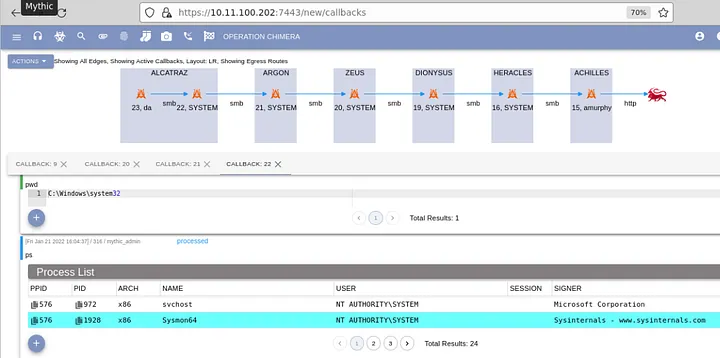
Research & Tradecraft
Apollo 2.0 — New Year, New Features
Introduction At the beginning of 2020, I took my first real foray into programming. Inspired by...
By: Dwight Hohnstein
Feb 2, 2022 • 8 min read
Read Post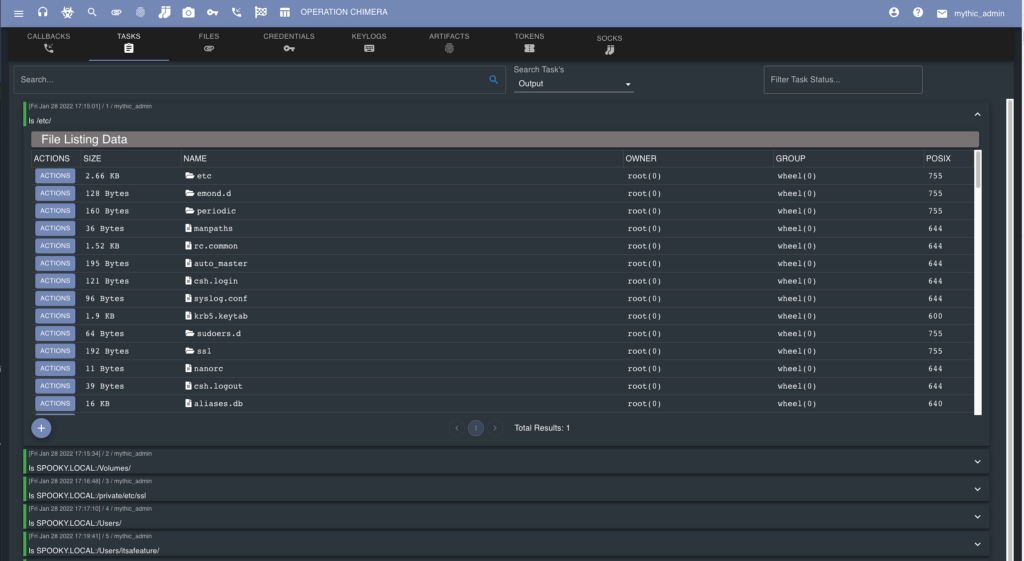
Research & Tradecraft
Mythic 2.3 — An Interface Reborn
Mythic 2.3 — An Interface Reborn New Mythic Search Mythic started off as a proof of concept, open source...
By: Cody Thomas
Jan 31, 2022 • 13 min read
Read Post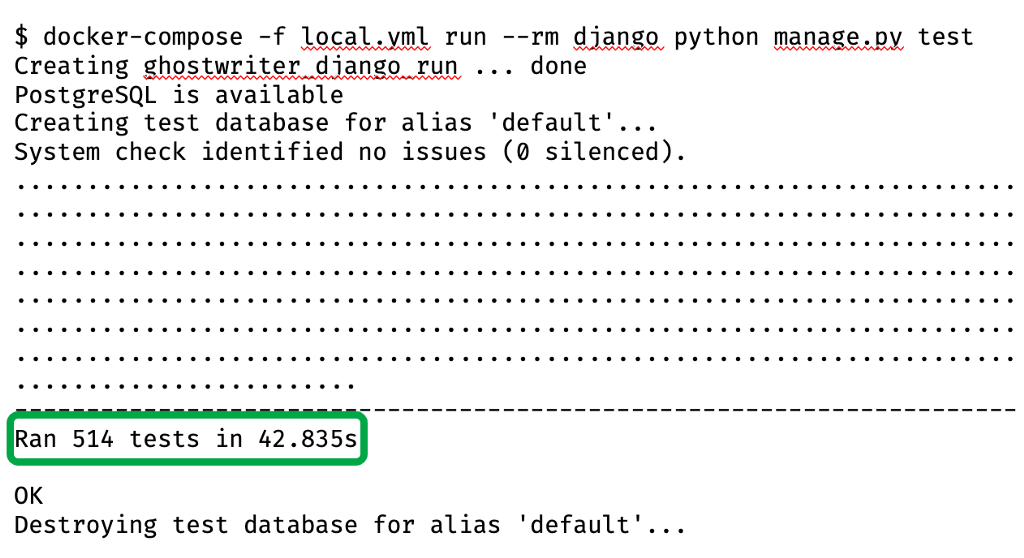
Research & Tradecraft
Ghostwriter: Looking Back at 2021
It has been a while since we last published details about the Ghostwriter project, but the...
By: Christopher Maddalena
Dec 22, 2021 • 6 min read
Read Post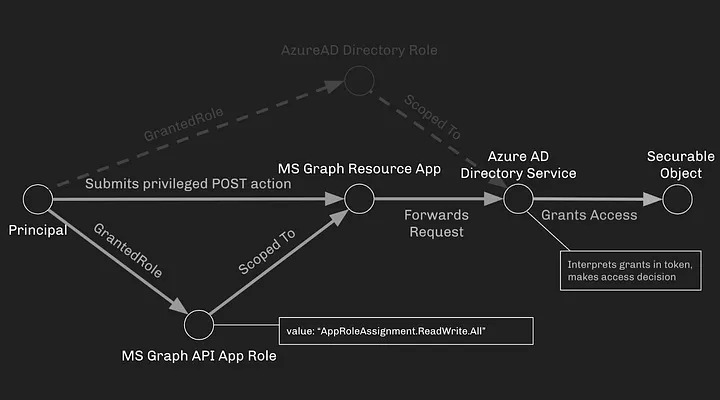
Research & Tradecraft
Azure Privilege Escalation via Azure API Permissions Abuse
Intro and Prior Work Microsoft’s Azure is a complicated system of principals, securable objects, and the...
By: Andy Robbins
Dec 1, 2021 • 13 min read
Read Post
Research & Tradecraft
Capability Abstraction Case Study: Detecting Malicious Boot Configuration Modifications
By: Michael Barclay
Nov 9, 2021 • 24 min read
Read Post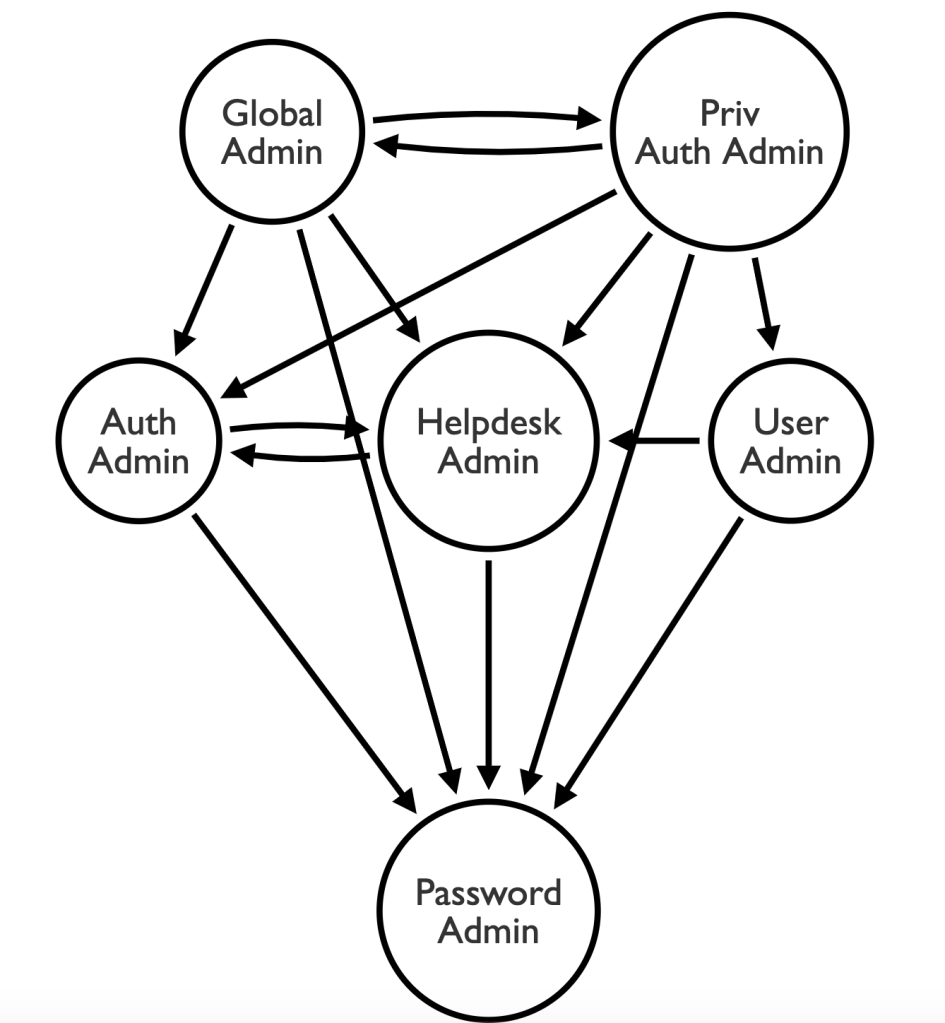
Research & Tradecraft
Azure Privilege Escalation via Service Principal Abuse
Intro and Prior Work On-prem Active Directory is here to stay, and so is Azure Active...