BloodHound 9.0 — Product Updates
Two weeks ago, we announced the new BloodHound Enterprise with OpenGraph extensions to extend attack path management to environments like Okta, GitHub, and Jamf. Along with this announcement, I’m pleased to share the release of BloodHound 9.0.
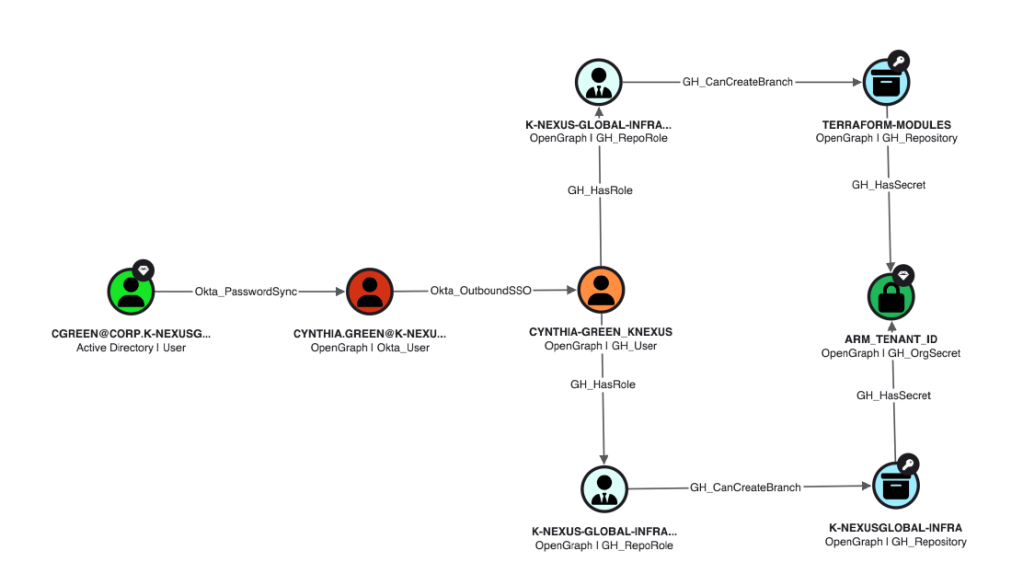
Attack paths move through SaaS apps, cloud platforms, endpoints, and identity providers; wherever relationships create opportunity. Attackers have been using our hyper-connected environments against us, abusing links across platforms that are impossible to find. Until now.
BloodHound 9.0 is about closing that gap.
With new capabilities like automated attack path analysis across Okta, Jamf, and GitHub, this release marks a step forward in how BloodHound models identity risk; expanding from directory-focused analysis to how identity risk unfolds across your environment.
Highlights
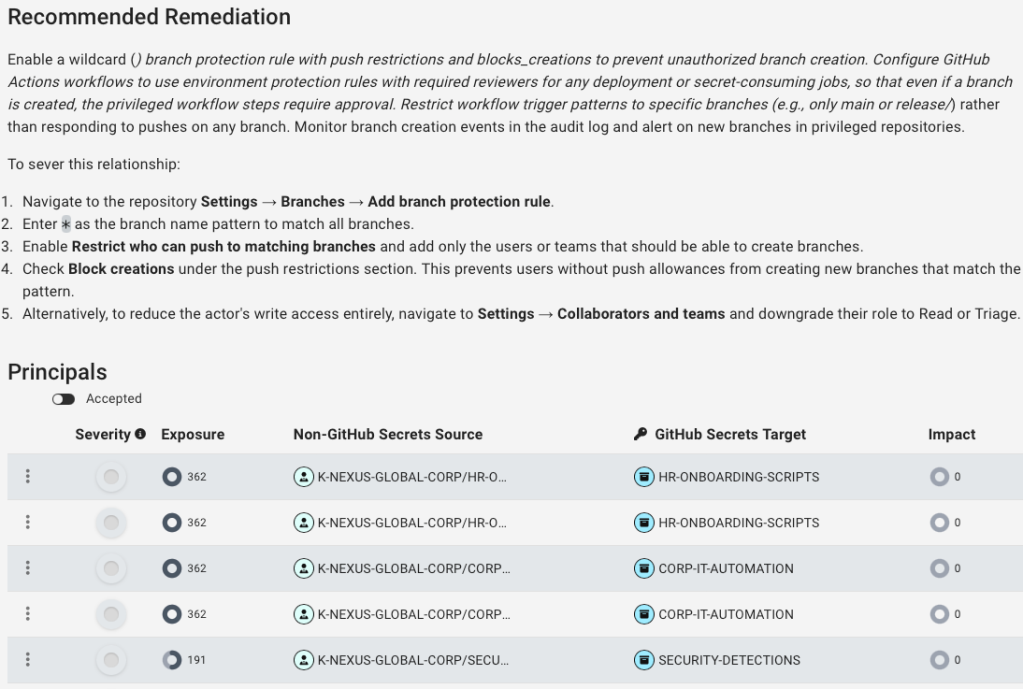
- Automated Attack Path Findings for Okta, Jamf, and GitHub: OpenGraph from these BloodHound Enterprise extensions now powers findings, metrics, and remediation guidance
- OpenHound: New framework for collecting and converting external data (GitHub, Okta, Jamf)
- OpenGraph Management: New UI and APIs for managing extensions and schemas
- Environment Targeted Access Control (ETAC): Scope user access by environment
- Graph & investigation improvements: Better readability, filtering, and query flexibility
- Hybrid data improvements: Cleaner Azure + AD relationship handling
OpenGraph & Data Expansion
Automated Attack Path Findings for Okta, Jamf, and GitHub in BloodHound Enterprise
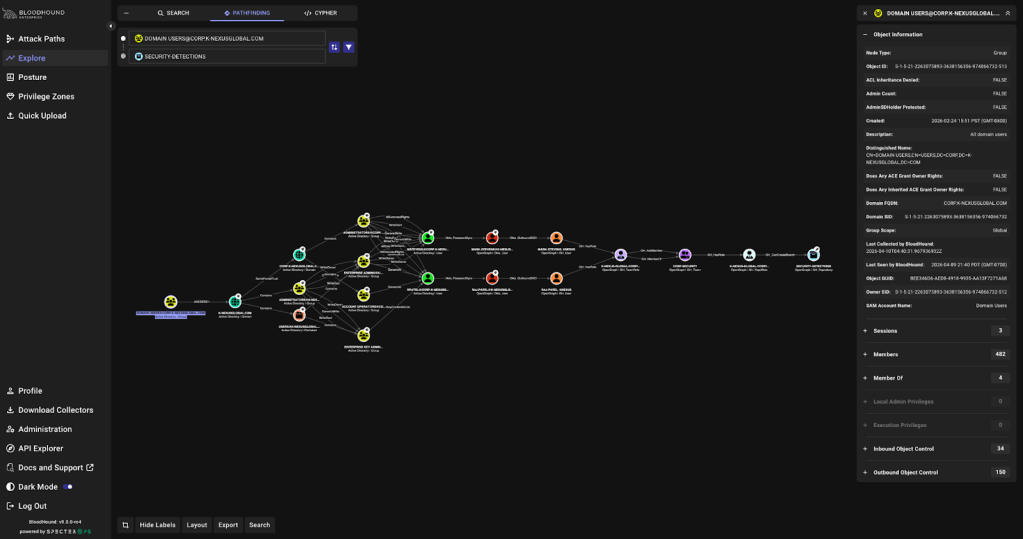
BloodHound Enterprise now automatically identifies and prioritizes attack path choke points across Okta, Jamf, and GitHub; delivering clear remediation guidance to eliminate risk and trend reporting to ensure it stays resolved.
Enterprise Extensions: Expanding Collection Across Key Platforms
BloodHound Enterprise customers now have access to enterprise-grade collection for recently announced extensions for Okta, Jamf, and Github.
Like the Enterprise versions of AzureHound and SharpHound, this allows customers to deploy continuous monitoring within these platforms to comprehensively map internal and cross-platform attack paths. This new collection method deploys via a container for flexibility within Enterprise accounts.
OpenHound: External Data Collection Framework
We’re also announcing OpenHound which introduces a standardized way to bring external system data into BloodHound. We’ve seen incredible excitement in OpenGraph since we released it last summer as authors create extensions to model attack paths in new platforms. We want to make this easier than ever by offering a standard way to connect to different platforms and format data for consumption by BloodHound.
OpenGraph authors can now concentrate more on the attack path logic than on the collection minutia:
- Collect and convert data from platforms like GitHub, Okta, and Jamf
- Built in Python using a consistent framework (DLT-based)
- Run as a CLI or containerized service
- Extend with custom collectors
This provides a repeatable way to expand the graph beyond AD and Entra ID. Expect a deep-dive blog post on OpenHound in the coming weeks.
OpenGraph Extension Management
New capabilities for managing OpenGraph schemas:
- Upload, update, and delete extensions via UI
- Define node types, edge types, and properties
- Ensure consistent ingestion of custom data
This release also exposes experimental OpenGraph Management APIs so you can evaluate and automate extension workflows:
| Method | Endpoint | Description |
| GET | /api/v2/extensions | Get a list of all OpenGraph extensions. |
| PUT | /api/v2/extensions | Upserts the OpenGraph extension. |
| DELETE | /api/v2/extensions/{extension_id} | Delete an OpenGraph extension. |
| GET | /api/v2/extension-edges | Get a list of all edge kinds across OpenGraph schemas. |
Access Control & Enterprise Scale
Environment Targeted Access Control (ETAC)
Configure access control policies in BloodHound Enterprise with Environment Targeted Access Control (ETAC), a new premium add-on that dynamically limits environment access for User and Read-only roles.
ETAC allows you to scope user access by environment, restricting which environments users can explore and analyze. This is especially useful in large, complex environments where users only need access to a specific subset of environments to perform their work.
ETAC introduces environment-level access scoping:
- Restrict users to specific environments
- Apply to User and Read-only roles
- Reduce unnecessary exposure in large deployments
Collection & Authentication
SharpHound Integrated Windows Authentication
- Supports ADFS with Integrated Windows Authentication (IWA)
- Aligns with Windows-native enterprise auth workflows
Explore & Investigation Improvements
Graph Readability
- Node labels include platform + type context
- Improved edge direction visibility
- Cleaner selection behavior
Table & Workflow Enhancements
- Drag-and-drop column ordering
- Column pinning and reset controls
- Better usability for large datasets
Search & Query Improvements
- Filter OpenGraph nodes by type
Export Improvements
- Timestamped filenames for graph exports
- Eliminates file overwrite conflicts
Data Quality & Performance
Azure Hybrid Data Improvements
- Removes unnecessary placeholder objects
- Only creates relationships when both sides exist
- Reduces graph churn and improves analysis time
Platform & Usability Updates
- Improved navigation sidebar behavior
- Accessibility improvements for assistive tech
- Posture metrics now show more precise values before abbreviation
- Improved custom date range validation for posture analysis
Fixes & Stability
This release includes fixes across:
- API and authorization handling
- Cypher query reliability and performance
- OpenGraph ingestion memory usage
- Privilege Zones and Posture UI issues
- AzureHound data accuracy
Closing
Identity risk isn’t confined to a single platform. And now neither is BloodHound.
With version 9.0, BloodHound continues to evolve into a platform for modeling, understanding, and eliminating identity attack paths across your entire environment.